Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter
641 Results Found
Solutions
Industry
371 - 380 of 641 results
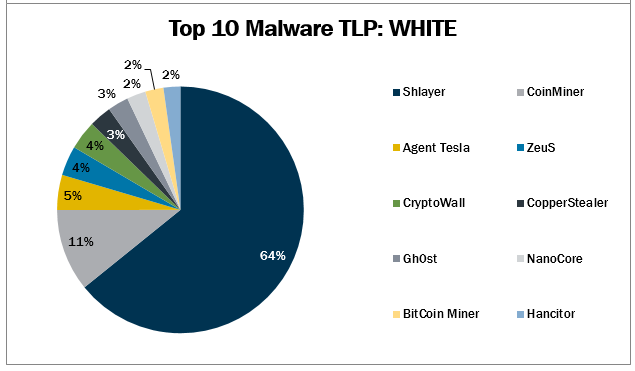
Published on 05.21.2021
In April 2021, the MS-ISAC observed CryptoWall, Gh0st, and NanoCore’s return to the Top 10, while BitCoin Miner made its first appearance. The To...
MS-ISAC
Published on 05.20.2021
Changes and advances in technology (and changes in workplace circumstances) have prompted a revamp of the CIS Community Defense Model (CDM). Set ...
CIS Controls
Published on 05.18.2021
By: Autum Pylant The moment we’ve all been waiting for is finally here. The Center for Internet Security (CIS) officially launched CIS Crit...
CIS Controls
Published on 05.11.2021
What are the benefits of cloud computing? Many organizations find that cloud service providers (CSPs) can meet their needs while providing a numb...
CIS Hardened Images
Published on 05.06.2021
Gartner forecasts that global public cloud end user spending will grow 23% in 2021. With the continuous increase in cloud computing, cloud securi...
CIS BenchmarksCIS Hardened Images
Published on 05.05.2021
We’re excited to announce our CIS Benchmarks May 2021 updates. These CIS Benchmark releases would not have been possible without the time and sup...
CIS BenchmarksCIS SecureSuite
Published on 05.04.2021
The Center for Internet Security (CIS) is excited to be part of RSA Conference 2021 – the world’s leading information security conference and exp...
CIS Controls
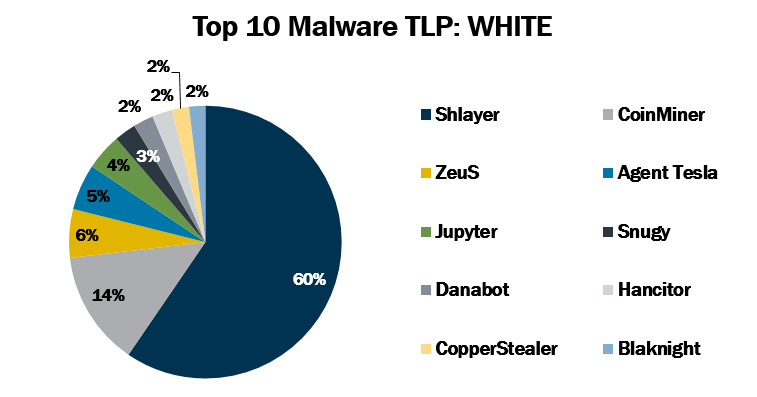
Published on 04.29.2021
In March 2021, the MS-ISAC observed Blaknight and Danabot’s return to the Top 10, while CopperStealer made its first appearance. The Top 10 Malwa...
MS-ISAC
Published on 04.27.2021
Securing your IT infrastructure can be a challenge, especially if you’re working in a regulated environment. Many compliance frameworks like, Def...
CIS Hardened Images
Published on 04.26.2021
Once your organization is secured, you’ll need to ensure that your environment doesn’t stray from its protected state. Configuration drift may be...
CIS SecureSuite
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More