All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1389 Results Found
Solutions
Industry
1151 - 1160 of 1389 results
Published on 04.23.2019
Helping U.S. State, Local, Tribal, and Territorial (SLTT) government entities respond to cyber incidents on a daily basis can be intense, but Val...
MS-ISAC
Published on 04.16.2019
Organizations providing cloud solutions to the U.S. government must comply with FedRAMP. CIS Hardened Images help Anitian automate FedRAMP compli...
CIS Hardened Images
Published on 04.09.2019
Want to maximize your cybersecurity with CIS-CAT Pro Dashboard? Watch this 30-minute presentation as the CIS technical team provides a walk-throu...
CIS Benchmarks
Published on 04.05.2019
What it is A password attack refers to any of the various methods used to maliciously authenticate into password-protected accounts. These attack...
MS-ISAC
Published on 04.04.2019
The CIS Critical Security Controls are internationally-recognized cybersecurity best practices for defense against common threats. They are a co...
CIS Controls
Published on 04.03.2019
Learn how CIS Critical Security Controls (CIS Controls) V7.1 and the CIS Sub-Controls map to NIST Cybersecurity Framework.
CIS Controls
Published on 04.03.2019
This spreadsheet provides an overview of the changes from CIS Critical Security Controls Version 7 to Version 7.1. Our goal is to provide a refer...
CIS Controls
Published on 04.03.2019
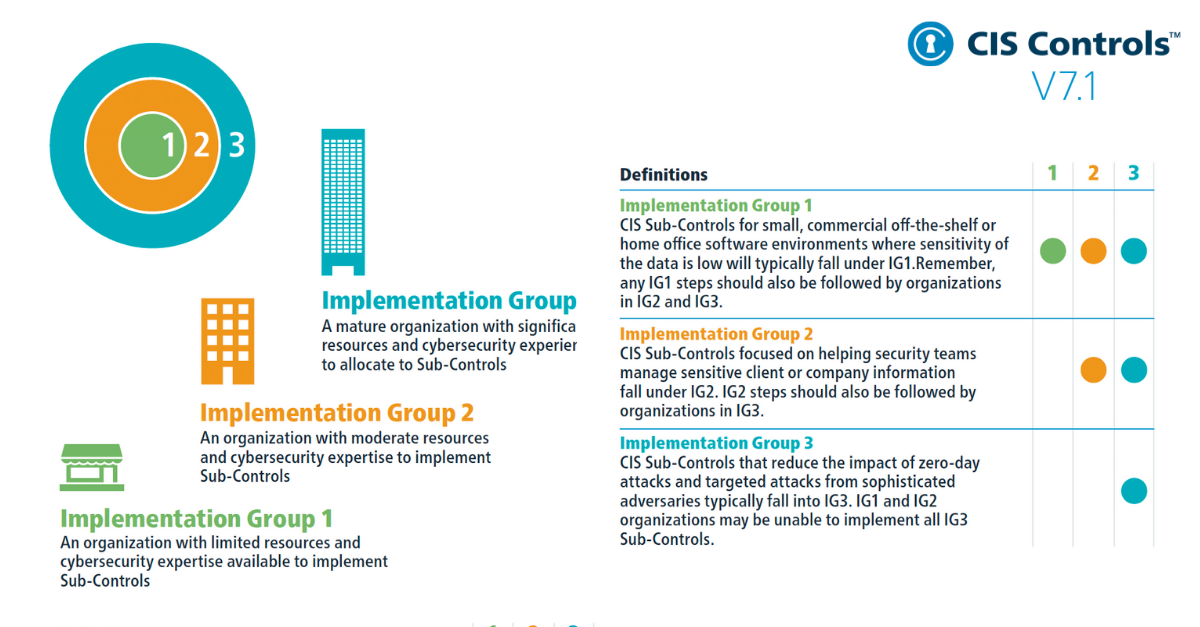
Discover how the CIS Sub-Controls break down into each Implementation Group. Implementation Groups provide a simple and accessible way to help or...
CIS Controls
Published on 04.02.2019
CIS Chief Technology Officer Brian Calkin predicted in our 2019 cybersecurity trends blog that organizations would continue to move to the cloud....
CIS Hardened Images
Published on 04.01.2019
Thursday, April 18, 2019 | 3:00pm EST The CIS Controls™ are a community-built set of prioritized cybersecurity guidance. They have been growing ...
MS-ISAC
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More