All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1389 Results Found
Solutions
Industry
1051 - 1060 of 1389 results
Published on 04.03.2020
Kids and teens around the country are staying home and adapting to a new virtual school environment. While the adjustment is fun for a while, the...
Published on 03.31.2020
The CIS Critical Security Controls Implementation Groups take a “horizontal” look across all of the CIS Controls and identify a set of Sub-Contro...
CIS Controls
Published on 03.30.2020
The Spring 2020 issue of Cybersecurity Quarterly includes articles highlighting the increase of workplaces going virtual and protecting the 2020 ...
CIS BenchmarksCIS ControlsCIS CyberMarketCIS Hardened ImagesCIS Services
Published on 03.30.2020
Google Cloud announced general availability of its Shielded VMs (virtual machines) at a breakout session during Google Cloud Next ‘19. As a resul...
CIS Hardened Images
Published on 03.24.2020
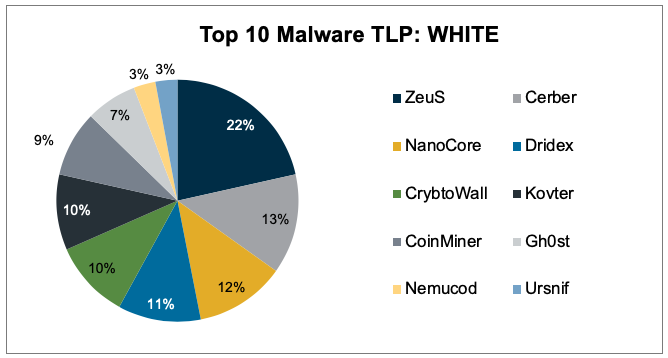
Top 10 Malware composition is very consistent with January 2020 with the exception of Ursnif. Nemucod remained, for the second month in a row, in...
MS-ISAC
Published on 03.19.2020
As the COVID-19 pandemic is forcing more and more companies to adjust their work schedules and move to telework environments, CIS remains committ...
CIS ControlsCIS SecureSuite
Published on 03.18.2020
Wednesday, March 25, 2020 2:00 pm EDT Chief Information Officers have a unique set of responsibilities in a pandemic. They far exceed the normal ...
MS-ISAC
Published on 03.17.2020
Does your organization struggle to prepare for cybersecurity audits, sometimes juggling multiple requirements? If so, you’re not alone. CIS takes...
CIS BenchmarksCIS ControlsCIS SecureSuite
Published on 03.14.2020
What it is: Signature-based and anomaly-based detections are the two main methods of identifying and alerting on threats. While signature-based d...
Published on 03.12.2020
With the COVID-19 (coronavirus) global pandemic, many employers are recommending additional telework to help keep employees safe and productive. ...
CIS Controls
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More