All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1387 Results Found
Solutions
Industry
851 - 860 of 1387 results
Published on 06.25.2021
Hospitals in Need of Cybersecurity STAT! The medical industry is an appealing target for cyber-attackers due to the vast personal information hos...
MS-ISAC
Published on 06.24.2021
Every October during Cyber Security Awareness Month (CSAM), the MS-ISAC conducts a national K-12 “Kids Safe Online” poster contest to encourage y...
MS-ISAC
Published on 06.23.2021
The CIS Benchmarks Community on CIS WorkBench is made up of subject matter experts, vendors, technical writers, and CIS SecureSuite Members from ...
CIS BenchmarksTechnology
Published on 06.22.2021
Thursday, June 24, 2021 | 1:00 pm EDT About this Webinar: Join cybersecurity experts Todd Fitzgerald and Tony Sager in the second of the SMB Cybe...
CIS Controls
Published on 06.22.2021
Previously presented on Thursday, July 8th | 2:00 pm EDT No matter how prepared, it’s an emotional and stressful experience managing a cyber data...
MS-ISAC
Published on 06.21.2021
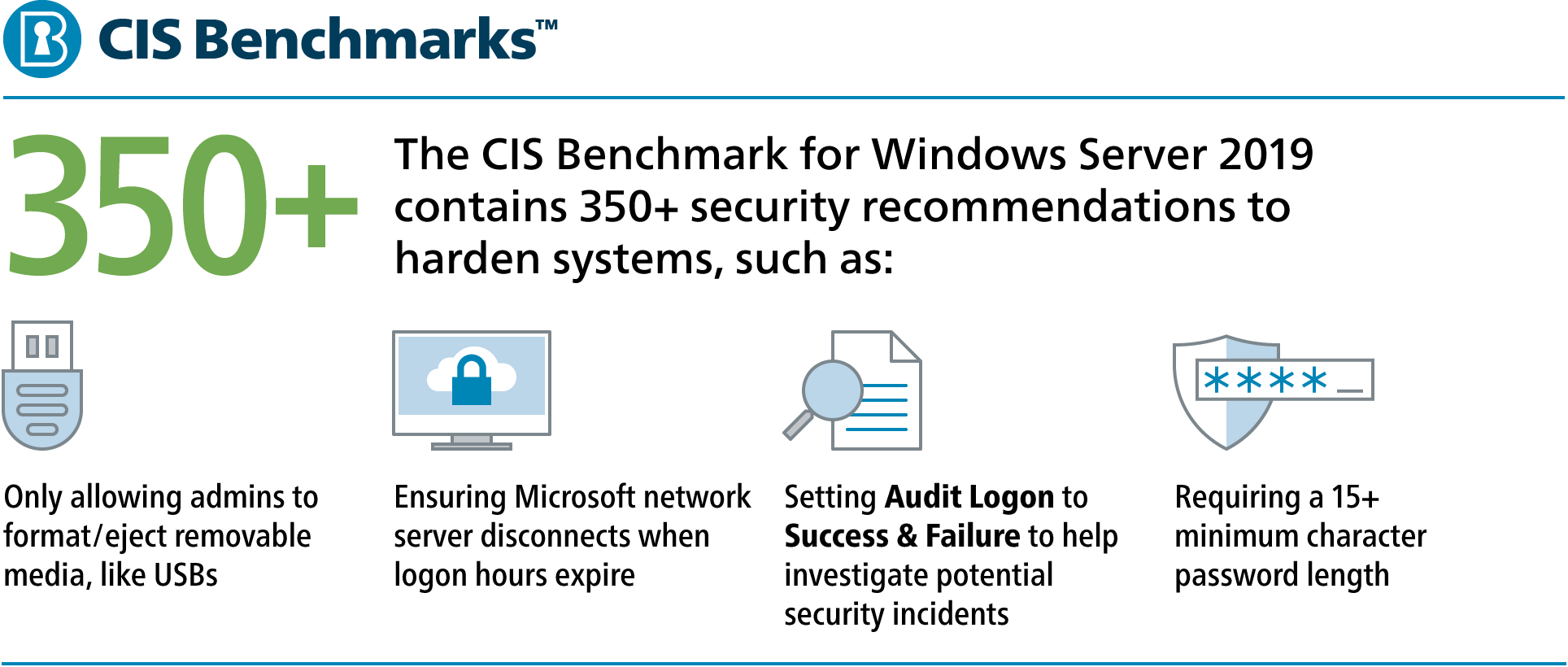
Cloud security is just as vital as on-premises security. Hundreds of security recommendations may exist to harden your Operating Systems (OS). Th...
CIS BenchmarksCIS Hardened ImagesCIS SecureSuite
Published on 06.17.2021
What does your cloud configuration look like? In many organizations, moving workloads to the cloud creates a more elastic technology infrastructu...
CIS BenchmarksCIS Hardened Images
Published on 06.16.2021
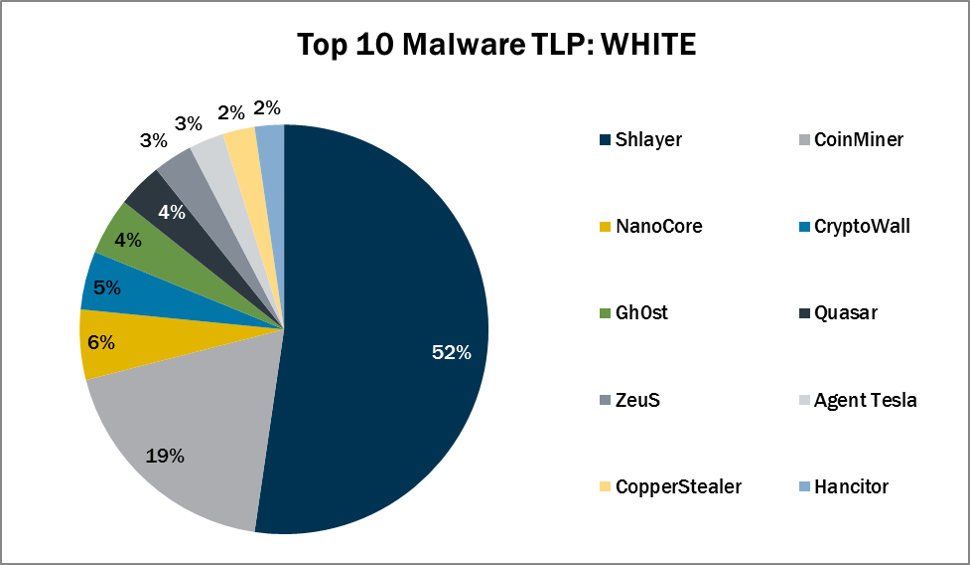
In May 2021, the MS-ISAC observed Quasar’s return to the Top 10. The Top 10 Malware variants comprise 75% of the total malware activity in May 20...
MS-ISAC
Published on 06.14.2021
Many offices are opening their doors and welcoming employees back to the workplace for the first time since the COVID-19 pandemic started. The tr...
CIS Controls
Published on 06.11.2021
Mitigating Risk: Information Security Governance Information security governance ensures that an organization has the correct information structu...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More