All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1378 Results Found
Solutions
Industry
781 - 790 of 1378 results
Published on 10.27.2021
This document contains mappings of the CIS Critical Security Controls and Safeguards to COBIT 19.
CIS Controls
Published on 10.25.2021
By Tony Sager, Senior VP and Chief Evangelist, CIS The term “cyber hygiene” has been around for at least a couple of decades, and is usually attr...
CIS ControlsCIS SecureSuite
Published on 10.22.2021
Chain of Custody is Crucial for Election Offices Chain of custody refers to the process or paper trail documenting the control or transfer of equ...
Published on 10.21.2021
Cybersecurity recruiting challenges: is there truly a lack of applicants, or are employers looking in the wrong places? CIS Senior Vice President...
Published on 10.21.2021
Just under 25% of the internet’s busiest websites – including Dropbox, Netflix, and WordPress.com – served or proxied NGNIX in July 2021, accordi...
CIS BenchmarksCIS Hardened Images
Published on 10.20.2021
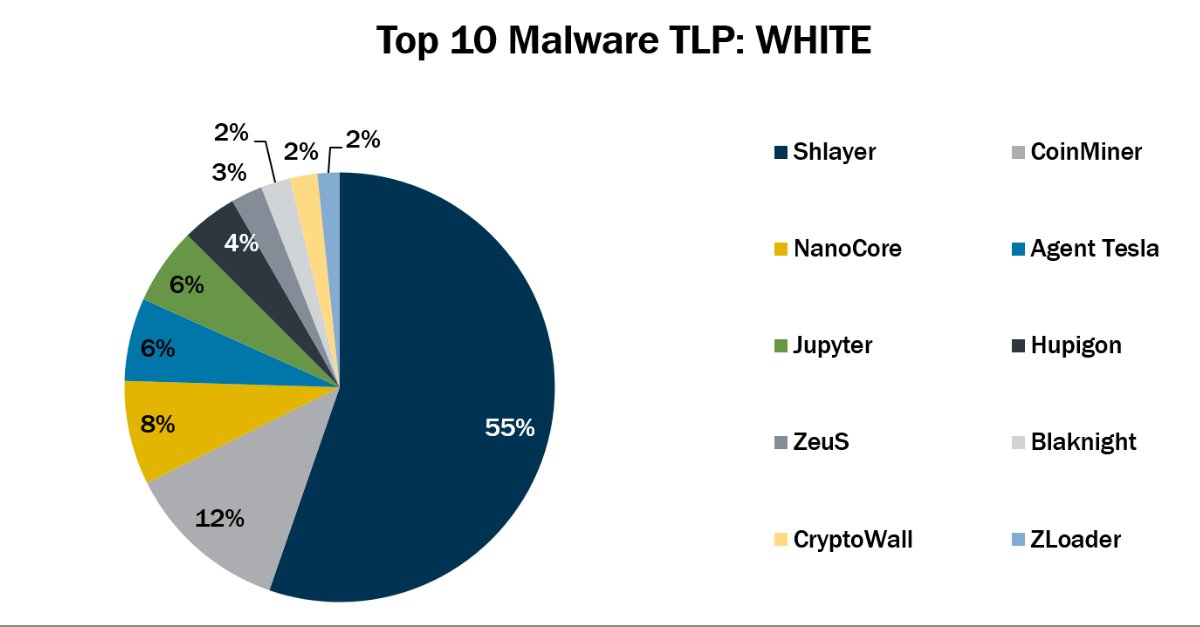
In September 2021, the MS-ISAC observed Jupyter’s return to the Top 10 Malware list. Additionally, ZLoader made its first appearance in the Top 1...
MS-ISAC
Published on 10.18.2021
By: Kathleen M. Moriarty, CIS Chief Technology Officer Let’s say you’re tasked with selecting a strong authentication solution for your organizat...
Published on 10.15.2021
By Adam Montville The Center for Internet Security (CIS) has a mission to improve the actual practice of cyber defense, and we do this, in part, ...
CIS BenchmarksCIS Controls
Published on 10.14.2021
The Center for Internet Security (CIS) and the Multi-State Sharing and Analysis Center (MS-ISAC) are proudly serving as partners for the Virtual ...
MS-ISAC
Published on 10.13.2021
In this edition of Cybersecurity Where You Are, CIS Chief Information Security Officer (CISO), Sean Atkinson welcomes Philippe Langlois of the Ve...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More