All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1387 Results Found
Solutions
Industry
1261 - 1270 of 1387 results
Published on 06.11.2018
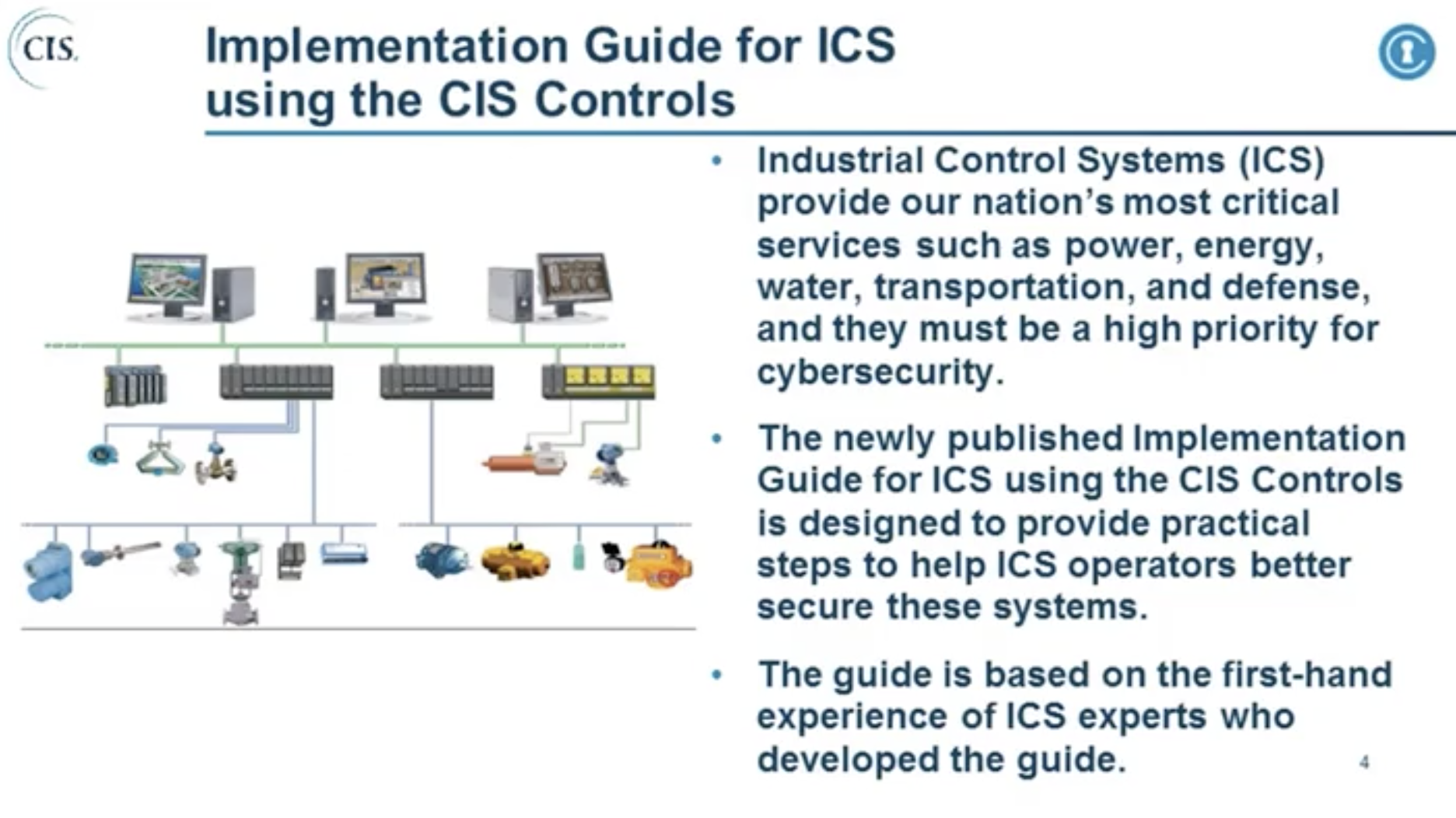
June 28, 2018 at 10:00 am EDT This webinar will discuss the CIS Controls Version 7 and the unique constraints and opportunities in Industrial Con...
CIS Controls
Published on 06.10.2018
Learn how one organization offers the CIS Controls as a questionnaire in a collaborative, online user experience.
CIS Controls
Published on 06.05.2018
Learn how a state credit union is using the CIS Controls cybersecurity best practices.
CIS ControlsFinance
Published on 06.05.2018
By Sean Atkinson, Chief Information Security Officer, CIS® Security is a journey, not a destination. It is important to understand that as securi...
CIS BenchmarksCIS Hardened ImagesCIS SecureSuite
Published on 05.29.2018
By Sean Atkinson, Chief Information Security Officer As organizations work to make internal company processes and personnel more secure it’s wort...
CIS Controls
Published on 05.19.2018
Learn how one full-service IT Solution Provider uses the CIS Controls to standardize and manage cyber assets.
CIS Controls
Published on 05.17.2018
The General Data Protection Regulation (GDPR) aims primarily to give control back to EU citizens and residents over their personal data while sta...
CIS BenchmarksCIS ControlsCIS Hardened ImagesCIS SecureSuite
Published on 05.15.2018
Let’s build on the harmonized combination of an organization’s risk manager and control framework described in my last blog post. Risk managers c...
CIS Controls
Published on 05.09.2018
Learn how the following steps can help organizations deal with a cyber incident. Establish Reliable Facts and a Way to Stay Informed Mobilize a R...
Published on 05.09.2018
Learn how SAM for Compliance helps organizations self-assess and manage their compliance to the CIS Controls.
CIS Controls
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More