All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1404 Results Found
Solutions
Industry
1201 - 1210 of 1404 results
Published on 01.28.2019
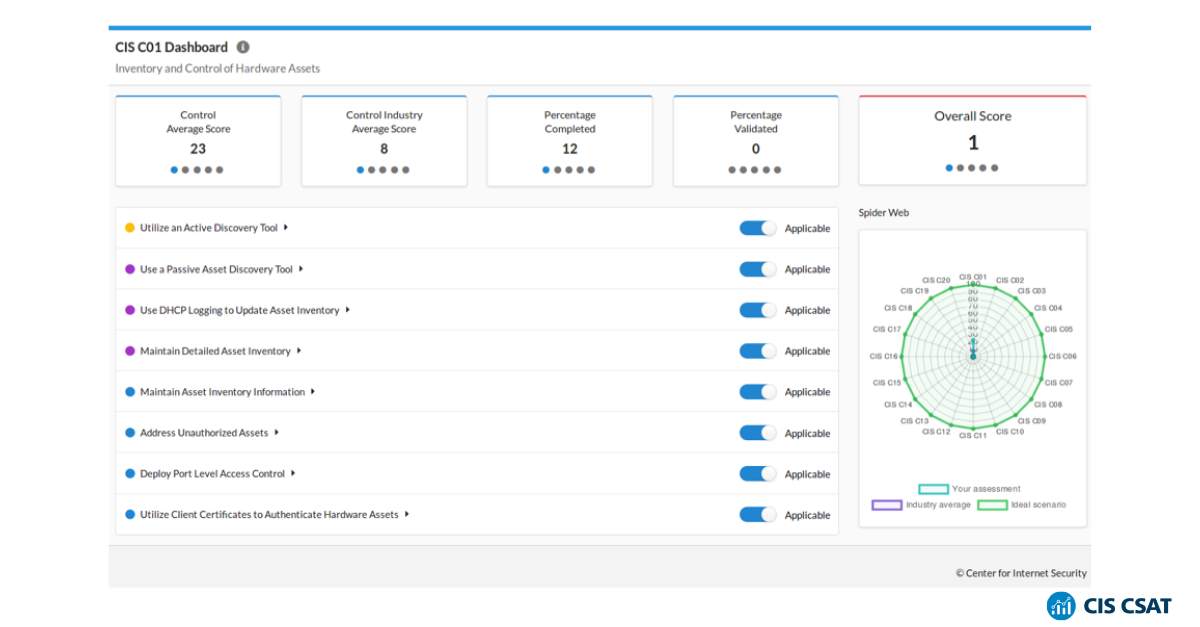
The CIS Critical Security Controls (CIS Controls) are a community-built set of prioritized cybersecurity guidance. They have been growing in popu...
CIS Controls
Published on 01.20.2019
Wednesday, February 20, 2019 | 3:00 pm EST Breaches are on the news seemingly weekly, as organizations are struggling to secure their data. Phish...
MS-ISAC
Published on 01.15.2019
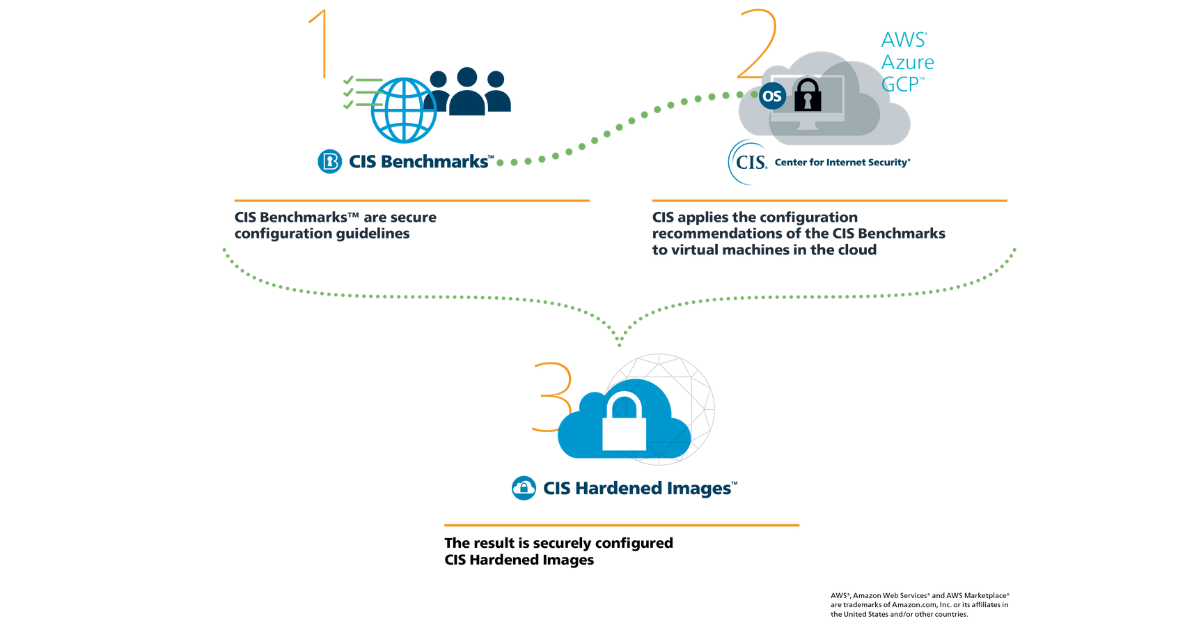
CIS just released two new CIS Hardened Images™ for operating systems on AWS Marketplace: Ubuntu Linux 18.04 and Amazon Linux 2. These images are ...
CIS Hardened Images
Published on 01.08.2019
Overview Remote Desktop Protocol (RDP) is a Microsoft proprietary protocol that enables remote connections to other computers, typically over TCP...
MS-ISAC
Published on 01.08.2019
At CIS our mission is simple – we want to help identify, develop, validate, promote, and sustain best practice solutions for cyber defense. One w...
CIS Benchmarks
Published on 01.07.2019
Overview EternalBlue is an exploit that allows cyber threat actors to remotely execute arbitrary code and gain access to a network by sending spe...
MS-ISAC
Published on 01.07.2019
What it is Doxing is the malicious identification and online publication of information about an individual. It can include Personally Identified...
MS-ISAC
Published on 01.03.2019
What it is Business Email Compromise (BEC) scams attempt to deceive organizations into sending money or employee’s personally identifiable inform...
MS-ISAC
Published on 01.03.2019
What it is A backup is a copy of the system or network’s data for file restoration or archival purposes. Backups are an essential part of a conti...
MS-ISAC
Published on 01.02.2019
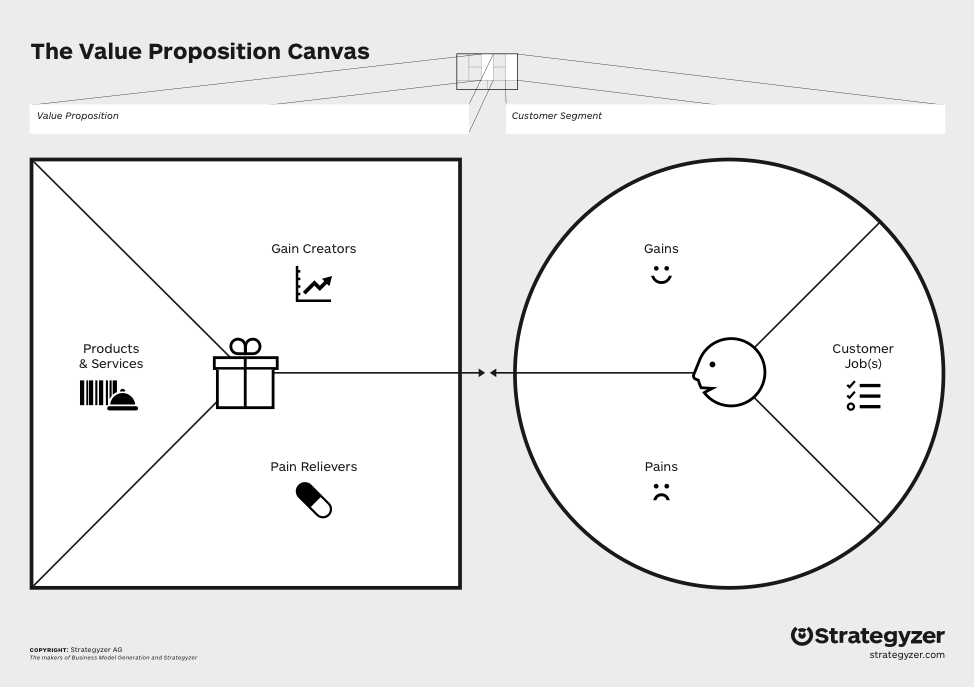
By Adam Montville, Chief Product Architect, CIS The theories Have you ever wondered how CIS decides which products to develop? Rather than reinve...
CIS BenchmarksCIS Controls
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More