All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1387 Results Found
Solutions
Industry
1121 - 1130 of 1387 results
Published on 08.06.2019
Being an Information Security Senior Auditor brings different challenges every day. Whether she’s helping conduct assessments or evaluating risk ...
CIS Controls
Published on 07.31.2019
When data is the lifeblood of your organization, ransomware hits like a heart attack. Are you prepared? Ransomware is a type of malware that bloc...
CIS Controls
Published on 07.16.2019
This document provides a detailed mapping of the relationships between CIS Critical Security Controls v7.1 and ISO 27001.
CIS Controls
Published on 07.10.2019
These documents contain examples of methods for tracking hardware, software, and sensitive information in an organization.
CIS Controls
Published on 07.10.2019
According to both Net Applications and Stat Counter, all versions of the Microsoft Windows operating systems combined represent well over 50% of ...
CIS Controls
Published on 07.10.2019
This guide provides detailed information on how to accomplish each of the CIS Sub-Controls within Implementation Group 1 (IG1). This guide builds...
CIS Controls
Published on 07.09.2019
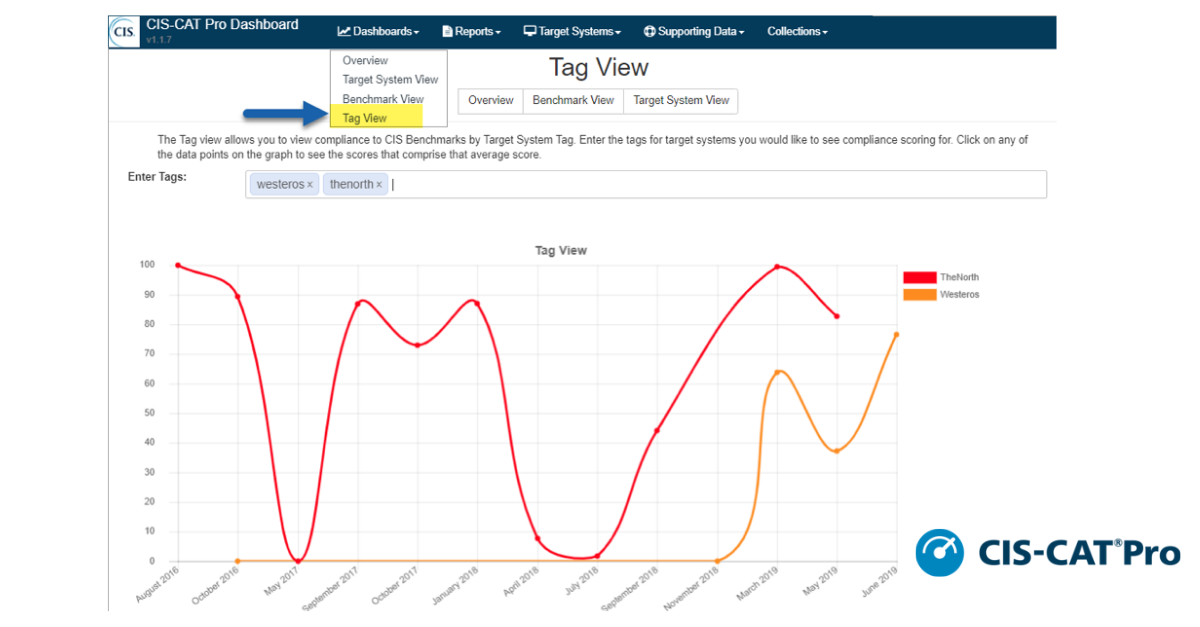
CIS SecureSuite® Members are receiving an update to CIS-CAT Pro Dashboard in v1.1.7. CIS-CAT Pro Dashboard is the companion tool to CIS-CAT Pro A...
CIS BenchmarksCIS SecureSuite
Published on 07.03.2019
Have you ever wanted to be part of a global security community? Want to help develop cybersecurity recommendations for new and emerging technolog...
CIS Benchmarks
Published on 07.02.2019
The CIS® team had a great experience at AWS re:Inforce from June 25-26, 2019 in Boston, MA. As AWS’ inaugural security conference, re:Inforce bro...
CIS Hardened ImagesCIS SecureSuite
Published on 06.28.2019
What it is: Internet Protocol (IP) is the communication standard used to uniquely identify systems on a computer network or across the internet. ...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More