Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter by Topic
584 Results Found
541 - 550 of 584 results
Published on 01.24.2018
Response Planning and the Year of Data PrivacyBy Sean Atkinson, Chief Information Security Officer, CIS Spectre, Meltdown, and response planning As I start my third week here at CIS, we find ...
Published on 01.12.2018
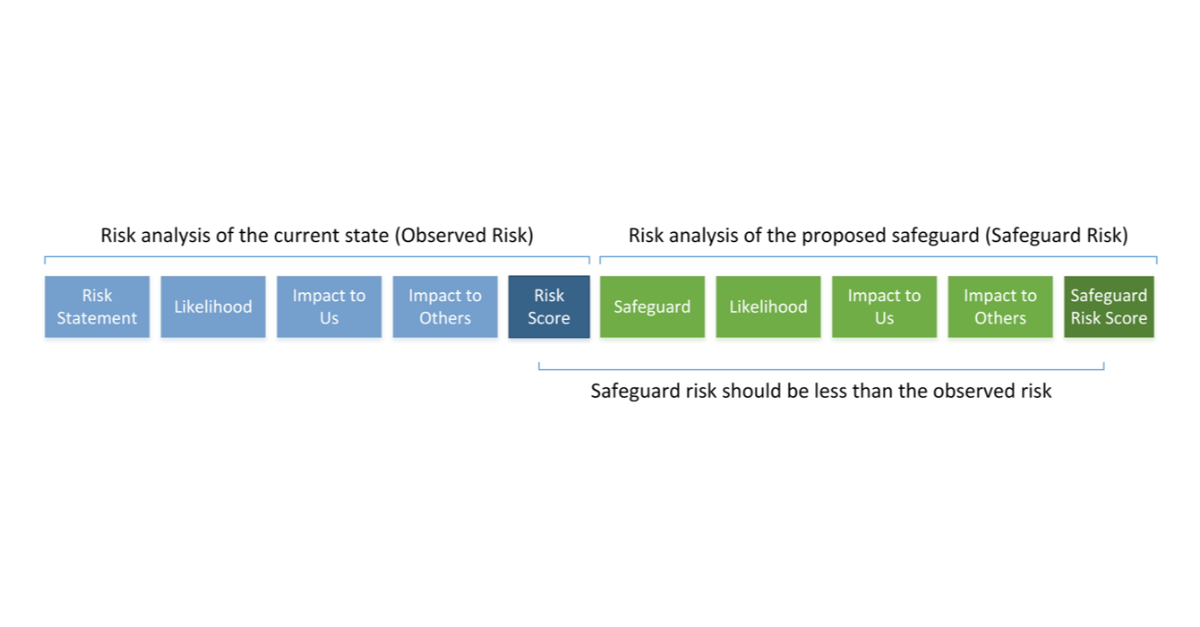
3 Things You’ll Learn Conducting a Cyber Risk Assessment with CIS RAMFor organizations who are conducting their first cyber risk assessment, it can be challenging to know where to start. CIS RAM (Center for Interne...
Published on 01.02.2018
Secure Configurations and the Power of SCAPBy Tony Sager, Senior Vice President, and Chief Evangelist Have you ever heard of Security Content Automation Protocols (SCAP)? SCAP is a method ...
Published on 12.26.2017
Unaccountable and thus Unattainable Network SecurityBy: Curtis Dukes, Executive Vice President Ransomware involves a request for a sum of money calculated to be less expense and trouble than trying...
Published on 12.19.2017
CIS Benchmarks Volunteer Spotlight: Paul CampbellThis month CIS is sharing an interview with CIS Benchmarks volunteer Paul Campbell. CIS values all of the volunteers who work hard to make sure t...
Published on 12.12.2017
Less Independence Day, more Groundhog Day: Building a good cyber defense routineBy Tony Sager, Senior Vice President, and Chief Evangelist Although it may seem fast-paced and glamorous, the cyber threat landscape is actually...
Published on 11.29.2017
Keeping a Watchful Eye on SoftwareMaintaining an accurate inventory of software is more than just eliminating potential employee distractions – it can also prevent potential legal...
Published on 11.08.2017
CIS Controls Volunteer Spotlight: James and Kelli TaralaCIS values all of the volunteers who work hard to make sure the CIS Benchmarks and CIS Controls reflect a global knowledge base of the latest kno...
Published on 11.06.2017
Update: CIS Microsoft Windows 10 Enterprise (Release 1703) Benchmark v1.0.0We are excited to announce we have released an update to the CIS Microsoft Windows 10 Benchmark. The updated CIS Microsoft Windows 10 Enterprise ...
Published on 10.30.2017
It is Time to Get Serious About Securing Our Nation’s Critical InfrastructureBy John M. Gilligan, Chairman and Interim Chief Executive Officer, CIS® An Escalating Threat Protecting this nation’s critical infrastructure is ...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More