Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter
655 Results Found
Solutions
Industry
401 - 410 of 655 results
Published on 04.08.2021
The Center for Internet Security (CIS) now offers two CIS Hardened Images, Ubuntu Linux 20.04 and Amazon Linux 2, on AWS Graviton2 processors. Am...
CIS Hardened Images
Published on 04.08.2021
The CIS Controls started as a grassroots activity over a decade ago to help enterprises focus on the most fundamental and valuable cybersecurity ...
CIS Controls
Published on 04.07.2021
A data breach can result in catastrophic consequences for any organization. Ensuring that your IT environment is safe from cyber threats can be a...
CIS SecureSuite
Published on 04.06.2021
CIS is excited to announce the release of the following CIS Benchmarks for March 2021. These CIS Benchmark releases would not have been possible ...
CIS BenchmarksCIS SecureSuite
Published on 04.05.2021
Part 1 in a series on Malware Summary TrickBot originated as a banking credential theft Trojan, but is now considered a modular malware enterpris...
MS-ISAC
Published on 04.02.2021
Amazon Web Services (AWS) continues to expand with new cloud products and services. The Center for Internet Security (CIS) responded with more re...
CIS Hardened Images
Published on 03.25.2021
We strive to keep the CIS Critical Security Controls relevant by updating them based on your feedback, evolving technology, and the ever-changing...
CIS Controls
Published on 03.22.2021
Article By: Autum Pylant, CIS Senior Product Communications Specialist We know that good “hygiene” is conducive to good health and cleanliness. A...
CIS Controls
Published on 03.20.2021
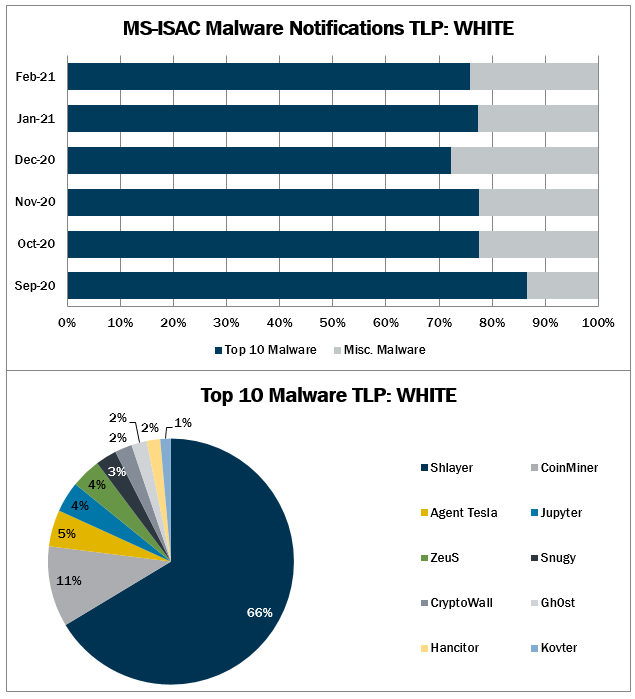
In February 2021, the MS-ISAC observed CryptoWall and Kovter’s return to the Top 10, while Hancitor and Jupyter made their first appearance. The ...
MS-ISAC
Published on 03.18.2021
Whether you are in the office or working from home, cybersecurity is everyone’s responsibility. Check out the infographic below for tips to stay ...
CIS BenchmarksCIS ControlsCIS CyberMarketCIS Hardened ImagesCIS Services
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More