Cyber Insurance Price Increases Highlight Ransomware Defense

We assess with moderate confidence that cybercrime and industry trends will continue to fluctuate relative to the evolving threat environment and the cyber insurance industry's ability to assess and mitigate cyber risk. This fluctuating relationship will place greater uncertainty on insurance coverage restrictions and place a greater responsibility on your organization to implement more rigorous enterprise cyber controls, as described at the end of this report, in order to attain adequate insurance over the next two years. Organizations unable to meet these standards independently are likely to look towards managed service providers, external organizations, or tools to bolster their security posture.
Ransomware's Impact on Cyber Insurance Affordability
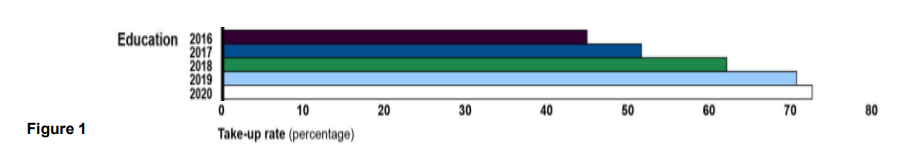
In 2020, we released a report disclosing how the number of organizations seeking cyber insurance coverage grew significantly over the previous years. For example, the U.S. Government Accountability Office (GAO) found that the education sector increased its adoption of cyber insurance over 25% between 2016 and 2020. (See Figure 1 below.)
These increases reflect the uptick in ransomware and high-profile cyber incidents leading up to 2020, including Ransomware-as-a-Service (RaaS) developments from groups likeLockBit and Conti. Cybercriminal groups such as these began demanding as much as $312,000 from their victims that year, according to Palo Alto Networks. That's 171% more than in 2019. For comparison, Palo Alto Networks found that RaaS groups issued an average demand of $925,162 during the first five months of 2022.
The spike in cyber insurance demand and increase in ransomware payments pushed insurance payouts above 70% of premiums, exceeding the break-even point. In response to this development, we assessed in our report that insurance companies would continue adjusting offerings to regain profitability, including elevating standards for customer cyber hygiene, increasing premiums, and lowering coverage limits – particularly for high-risk sectors like healthcare and education. We assessed that these elevated requirements would put increased strain on decision makers who opt for cyber insurance, as they would be required to meet increasingly-demanding cybersecurity standards to qualify for affordable coverage.
Alternatively, we noted that insurance companies could follow the lead of AXA who responded to pressure from French justice and cybersecurity officials by halting reimbursements for ransomware payments among some of their clients, as reported by SecurityWeek. We observed that this move could also involve decreasing payouts due to the high cost of fully rebuilding systems if the insured organization opted not to pay. This would require victims of ransomware to rebuild with a reduced payment or pay the ransom without insurance support. Additionally, this will likely drive a second-order impact where cybercriminals decrease ransom demands to meet victims' increased unwillingness to pay hefty sums.
Finally, we acknowledged a high impact but low probability alternative scenario where lawmakers decide to prohibit ransomware payments. In the short-term, we pointed out that this would necessitate costly rebuilds of entire systems or permanent data loss following a breach. Long-term, however, we saw that this would have a dramatic impact on the ransomware marketplace, as cybercriminals (aware their ransom demands will not be met) would be forced to find alternative means to earn money through cybercrime.1
Revisiting Our Assessment Two Years Later
Now roughly a year and a half since our initial report, we observe that the trend of decreasing cyber insurance affordability initially held up but shifted in early 2022. In its 2022 State of the Market report, Risk Strategies found that steep rate increases in cyber insurance began to stabilize largely due to organizations improving their cyber maturity, no doubt influenced in part by stricter policies from insurance underwriters. Global insurance broker and risk advisor Marsh confirmed this trend, finding that insurance rate increases had on average declined nearly 80% from December 2021 to July 2022. Beyond the impact of improved controls and insurer policies, recent open-source reporting indicates organizations are increasingly refusing to pay ransoms. As reported Bleeping Computer, this is resulting in a 40% decrease in global ransomware payouts.
Despite the recent downturn in insurance rates, we assess evolving cybercriminal activity is likely to once again drive rates upward, albeit at a slower pace than pre-2022 levels, over the next two years. The threat environment will continue to feature CTAs' evolving TTPs through means like RaaS and automated tools. Insurers, in turn, will continue to adapt to meet the market, but given the overall trends, the threat environment will place a greater responsibility on organizations to maintain contingency plans to prepare for the likelihood of an intrusion that could cost as much as millions in ransom or recovery. That doesn't even account for risks of litigation, loss of data, and reputational costs. To put those risks into perspective, a Blackberry survey found that 60% of business would reconsider partnerships with another organization lacking comprehensive cyber insurance.
In some cases, organizations will likely even contemplate self-insuring. When costs and coverage become prohibitive for entities, some will look to allocate additional capital to fill gaps or entirely self-source insurance. Despite the upside of self-setting coverage limitations and savings on premiums, many organizations would find this avenue difficult or unfeasible due to challenges in assessing and quantifying risk as well as ensuring they have adequate cash-on-hand to cover the impact of a major incident.
Focus on Cybersecurity Defenses
Rising costs and uncertainty in assessing organizations' risk profiles may eventually lead the federal government to intervene. This would likely include providing comprehensive data for insurers and a degree of risk transfer through a rainy-day fund stored in the event of a catastrophic industry-shaking incident. The GAO, which has been tracking trends in the cyber insurance market over the last several years, recently went so far as to officially recommend that the federal government review the current state of the industry for possible intervention.
Regardless of whether government intervention follows, however, you can take this time to review your current policies and ensure that your defensive controls are sufficient to meet insurer requirements and stand up against against increasingly sophisticated ransomware attacks. Specifically, you should implement controls comparable to the CIS Critical Security Controls (CIS Controls). These security measures can help put you in the best position to minimize your cyber risk and associated costs. As revealed by our Community Defense Model (CDM) v2.0, you can use Implementation Group 1 (IG1) of the CIS Controls to mitigate at least three-quarters of MITRE ATT&CK (sub-)techniques associated with ransomware and other threats.
Lay a foundation for defending against ransomware and other common cyber threats with IG1.
About the Author: The Cyber Threat Intelligence (CTI) team at the Multi-State Infrastructure Information Sharing and Analysis Center (MS-ISAC) functions as the premier CTI source for all U.S. State, Local, Tribal, and Territorial (SLTT) entities and election offices. With decades of combined experience in all types of industries, the CTI team pushes out curated SLTT-centric threat intelligence reporting as well as malicious indicators via near real-time threat feeds. This information helps SLTTs anticipate and proactively defend against emerging cyber threats and shifts in adversarial tactics, techniques, and procedures. Additional information: team tradecraft and indicator feeds.
1 The CTI Team used Multiple Scenarios Generation (MSG) Structured Analytic technique to assess the most likely and High Impact/Low Probability scenarios. Multiple Scenarios Generation (MSG) Structured Analytic from http://www.pherson.org/wp-content/uploads/2013/11/02.-The-Tradecraft-of-Warning-Paper_FINAL.pdf.
As of June 23, 2025, the MS-ISAC has introduced a fee-based membership. Any potential reference to no-cost MS-ISAC services no longer applies.
