All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1387 Results Found
Solutions
Industry
1171 - 1180 of 1387 results
Published on 02.26.2019
CIS® is home to the Multi-State Information Sharing and Analysis Center® (MS-ISAC®). It’s the go-to resource for cyber threat prevention, protect...
MS-ISAC
Published on 02.21.2019
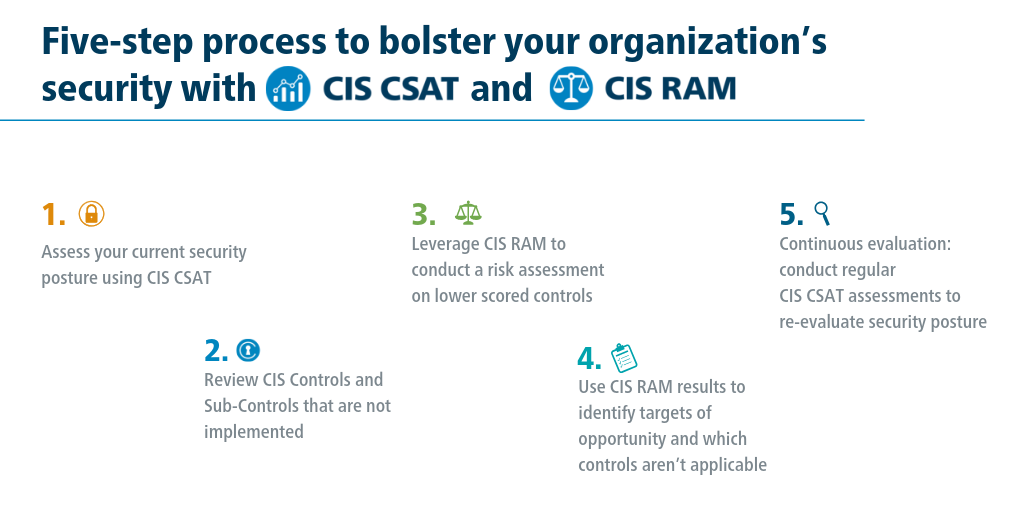
By Sean Atkinson, Chief Information Security Officer, and Phil Langlois, CIS Controls Technical Product Manager The CIS Controls are used by orga...
CIS Controls
Published on 02.20.2019
Learn more about what the EI-ISAC accomplished in 2018.
Published on 02.15.2019
What it is The National Institute of Standards and Technology (NIST) National Initiative for Cybersecurity Education, Cybersecurity Workforce Fra...
MS-ISAC
Published on 02.15.2019
By Curtis Dukes, Executive VP and GM – CIS Security Best Practices The recently released House Oversight and Government Reform Committee Congress...
CIS Controls
Published on 02.12.2019
Working with an army of global adopters and cybersecurity experts, the CIS Controls team created a cloud security companion guide to help secure ...
CIS Controls
Published on 02.12.2019
In this document, we provide guidance on how to apply the security best practices found in CIS Critical Security Controls Version 7 to any cloud ...
CIS Controls
Published on 02.11.2019
The CIS Controls Cloud Companion Guide provides guidance on how to apply the security best practices found in CIS Controls Version 7 to any cloud...
CIS Controls
Published on 02.08.2019
As cryptocurrency sees increased adoption, state, local, tribal, and territorial (SLTT) governments are encountering malware designed to steal or...
MS-ISAC
Published on 02.08.2019
State, local, tribal, and territorial (SLTT) governments are frequently targeted by Business Email Compromise (BEC) scams that attempt to deceive...
MS-ISAC
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More