All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1389 Results Found
Solutions
Industry
1031 - 1040 of 1389 results
Published on 05.22.2020
The CIS Critical Security Controls v7.1 are mapped to the Cybersecurity Maturity Model Certification (CMMC) levels to help organizations required...
CIS Controls
Published on 05.21.2020
Verizon’s Data Breach Investigations Report (DBIR) provides an annual analysis of security incidents and data breaches. The information and analy...
CIS ControlsMS-ISAC
Published on 05.19.2020
The thirteenth Verizon Data Breach Investigations Report (DBIR) was released on May 19, 2020. Verizon may be most well-known for their leadership...
CIS Controls
Published on 05.19.2020
Spread cybersecurity awareness in your office!
MS-ISAC
Published on 05.19.2020
Cybersecurity posters brought to you by the MS-ISAC
MS-ISAC
Published on 05.19.2020
What it is: Cyber threat indicator sharing is the practice of exchanging actionable threat intelligence between organizations. The information sh...
Published on 05.15.2020
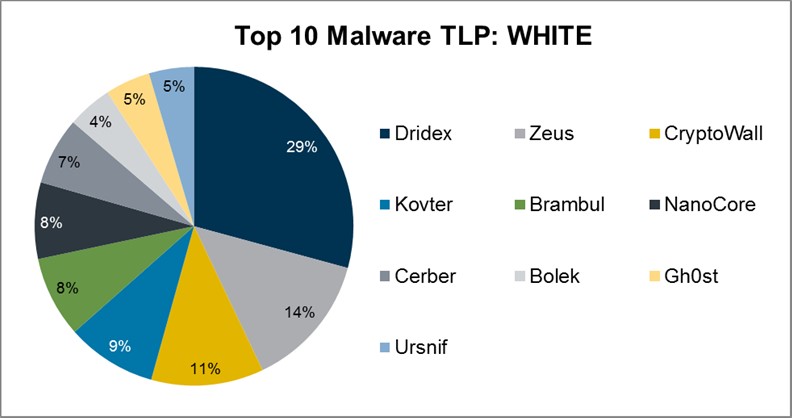
Top 10 Malware composition was fairly consistent with March 2020 with the exception of Bolek and Brambul. Overall, the Top 10 Malware variants co...
MS-ISAC
Published on 05.11.2020
CIS Oracle Database 12c Benchmark v3.0.0 This CIS Benchmark was released with the following improvements: Guidance was added to existing and new ...
CIS BenchmarksTechnology
Published on 05.06.2020
In addition to being costly and troublesome, the continued use of unsupported technologies can expose your organization to security risks. Patchi...
CIS BenchmarksTechnology
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More