All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1410 Results Found
Solutions
Industry
1 - 10 of 1410 results
Published on 06.05.2026
The 2026 Verizon DBIR highlights how CIS Controls and CIS Benchmarks strengthen cybersecurity hygiene and defend against today’s top attack...
CIS BenchmarksCIS ControlsMS-ISACEducationHealthcare
Published on 06.02.2026
Listen to our podcast as experts separate fact from fiction around Mythos AI and other AI-driven vulnerability discovery tools.
Published on 06.02.2026
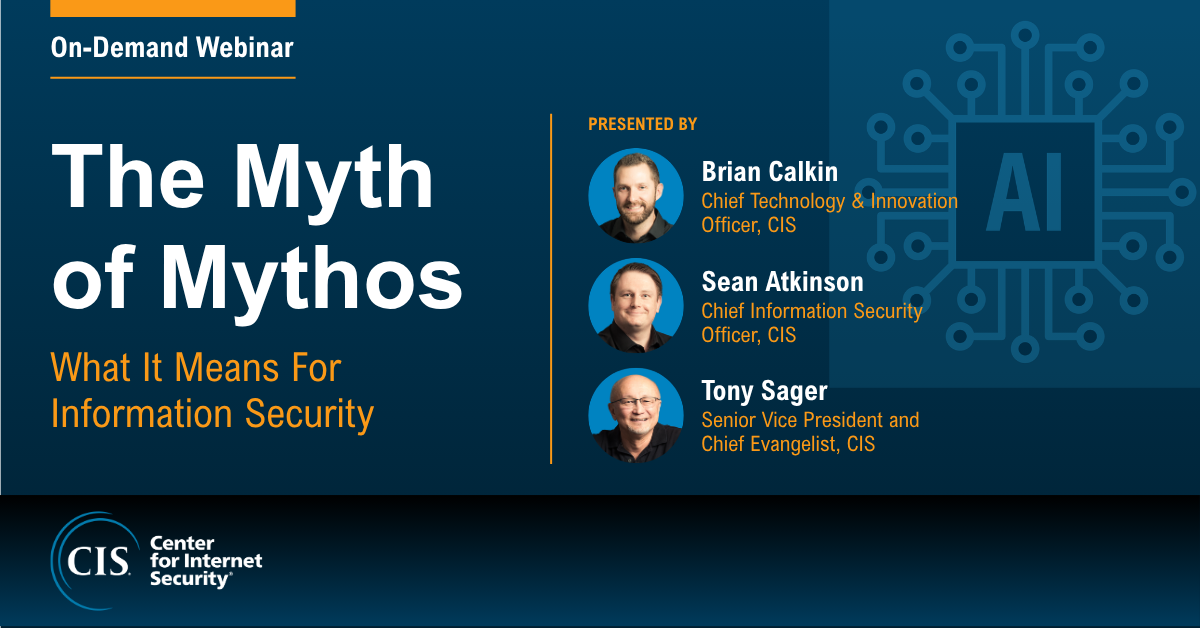
This webinar will explain why, despite the increased speed and scale, AI does not fundamentally change the security challenge. Zero‑days aren’t n...
Published on 05.29.2026
The Verizon Data Breach Investigations Report (DBIR) is one of the most trusted sources of cybersecurity threat intelligence in the industry, dra...
CIS Controls
Published on 05.27.2026
Senteon uses its CIS SecureSuite® Product Vendor Membership to simplify customers' system hardening efforts in less time. Read on to see how.
Published on 05.26.2026
Curious about the present and future of AI-enabled pentesting? Hear Ed Skoudis of SANS Technology Institute share his thoughts on our podcast.
Published on 05.19.2026
Listen to our podcast episode for top insights of the 2026 DBIR and how CIS collaborated with Verizon to inform the publication's findings.
Published on 05.19.2026
Organizations worldwide rely on CIS Benchmarks® as the trusted foundation for secure configuration and audit readiness programs.
Published on 05.18.2026
The following CIS Benchmarks and CIS Build Kits have been updated or recently released. We've highlighted the major updates below.
CIS Benchmarks
Published on 05.15.2026
Password managers can significantly reduce the risk of security breaches caused by weak, reused, or forgotten passwords. Learn more.
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More





.png?h=628&iar=0&w=1200&rev=cd7f166595a24002a90e1ba8c43d461b&hash=A9B35A15DF0D1084B14EF5484D31AB5D)
