Showing results 1 - 20 of 2322 for "NiftByte Compare the Best Prices for CD Keys and Steam Keys"
BLOG POST - https://www.cisecurity.org/insights/blog/how-to-secure-your-online-identity-with-security-k...
How to Secure Your Online Identity with Security Keys
An intern with our CTO office embarked on a short project to protect her accounts with security keys. Here's what her experience was like....
MEDIA MENTION - https://www.cisecurity.org/about-us/media/media-mention/telehealths-emergence-and-the-keys-...
Telehealth’s Emergence and the Keys to Security in 2021
Data encryption, network hardening, and automated threat hunting provide a basis for defense in depth for healthcare organizations and telehealth in 2...
MEDIA MENTION - https://www.cisecurity.org/about-us/media/media-mention/these-devices-can-be-a-lifesaver-fo...
These devices can be a lifesaver for finding your keys
Apple's Airtag and similar devices like Tile are marketed as useful tools for people to keep track of their belongings, from house keys to luggage and...
WHITE PAPER - https://www.cisecurity.org/insights/white-papers/security-primer-cryptocurrency
Security Primer – CryptoCurrency
As cryptocurrency sees increased adoption, state, local, tribal, and territorial (SLTT) governments are encountering malware designed to steal or mine...
SPOTLIGHT - https://www.cisecurity.org/insights/spotlight/ei-isac-cybersecurity-spotlight-encryption
Election Security Spotlight – Encryption
What it is Encryption is the process whereby data is converted from a readable form (i.e., plaintext), to an encoded form (i.e., ciphertext). This enc...
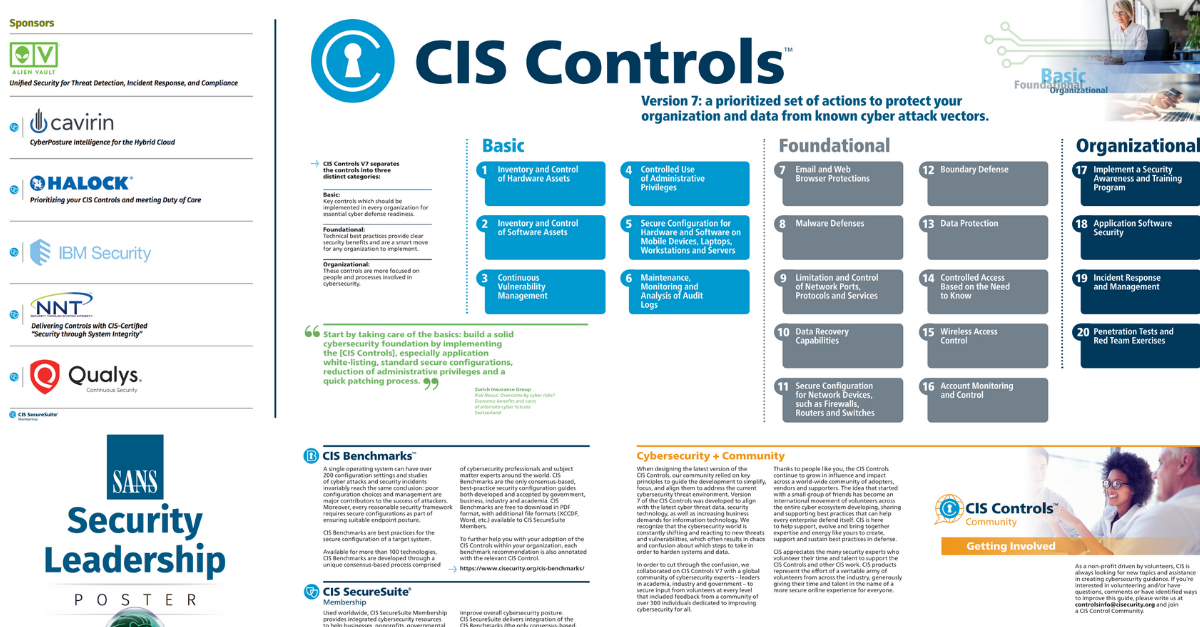
WHITE PAPER - https://www.cisecurity.org/insights/white-papers/cis-controls-v7-poster
CIS Controls V7 Poster
CIS Controls V7 is a prioritized set of actions to protect your organization and data from known cyber attack vectors. Learn about the basic, foundati...
WHITE PAPER - https://www.cisecurity.org/insights/white-papers/security-primer-ryuk
Security Primer – Ryuk
Overview Ryuk is the most prevalent ransomware variant in the state, local, tribal, and territorial (SLTT) government sector. It is the number one rep...
SPOTLIGHT - https://www.cisecurity.org/insights/spotlight/ei-isac-cybersecurity-spotlight-cryptocurrenc...
Election Security Spotlight – Cryptocurrency
What it is Cryptocurrency refers to a form of currency that is only available in a digital format. It relies on cryptographic algorithms to record fin...
BLOG POST - https://www.cisecurity.org/insights/blog/ransomware-impacts-and-defense-controls
Ransomware Impacts and Defense Controls
When data is the lifeblood of your organization, ransomware hits like a heart attack. Are you prepared? Ransomware is a type of malware that blocks ac...
PAGE - https://www.cisecurity.org/text-feed-help
Text Feed Help
Text Feed The MS-ISAC Cyber Alert Level Indicator is available as a text-based feed. The following fields are available in the text feed: Alert Level ...
MEDIA MENTION - https://www.cisecurity.org/about-us/media/media-mention/learn-some-key-cloud-workload-prote...
Learn Some Key Cloud Workload Protection Best Practices
Learn key practices to protect cloud workloads when using VMs, endpoints, or containers. And, consider the best means for building a fruitful feedback...
WHITE PAPER - https://www.cisecurity.org/insights/white-papers/cis-primer-emergency-preparedness-for-cybe...
MS-ISAC Security Primer – Emergency Preparedness for Cyber Infrastructure
Overview Disaster preparation should include protecting cyber assets. The Multi-State Information Sharing & Analysis Center (MS-ISAC) is providing the...
BLOG POST - https://www.cisecurity.org/insights/blog/why-oauth-is-so-important-an-interview-with-justin...
Why OAuth is so Important: An Interview with Justin Richer
This is the third article in this series by Kathleen Moriarty, CIS Chief Technology Officer. In this article, Moriarty interviews Justin Richer, an in...
BLOG POST - https://www.cisecurity.org/insights/blog/top-videoconferencing-attacks-and-security-best-pr...
Top Videoconferencing Attacks and Security Best Practices
Videoconferencing has become a routine part of everyday life for remote workers, students, and families. Yet widespread adoption of this technology ha...
BLOG POST - https://www.cisecurity.org/insights/blog/cis-security-best-practices-cooperative-product-de...
CIS Security Best Practices Cooperative Product Development
By Adam Montville, Chief Product Architect, CIS The past few years have been an interesting ride within Security Best Practices, the CIS group respons...
PRESS RELEASE - https://www.cisecurity.org/about-us/media/press-release/center-for-internet-security-named-...
Center for Internet Security Named Among 2024 Best Companies to Work for in New York
Cybersecurity nonprofit earns the distinction for the fifth consecutive year....
CASE STUDY - https://www.cisecurity.org/insights/case-study/bank-relies-on-industry-recommended-cybersec...
National Bank Relies on Industry-Recommended Cybersecurity Best Practices
Learn how one financial institution uses the cybersecurity best practices included in CIS SecureSuite Membership to bolster their cyber defenses....
CASE STUDY - https://www.cisecurity.org/insights/case-study/how-to-choose-a-cybersecurity-consultant-wha...
How to Choose a Cybersecurity Consultant: What are their Security Best Practices?
Learn how one cybersecurity consulting organization uses the security best practices of CIS SecureSuite to help clients defend against cyber threats....