The Changing Threat Environment
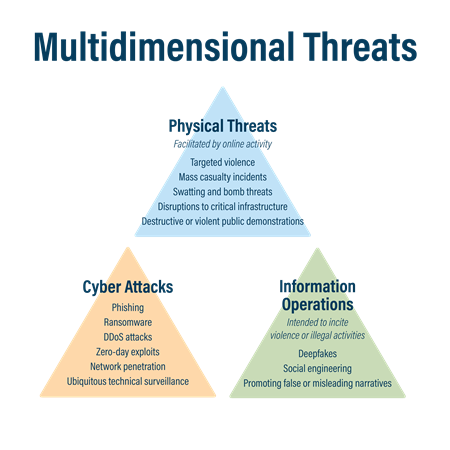
Threat actors are increasingly using multidimensional threats, or the blending of cyber, physical, and information operations, to advance their objectives.
Hostile foreign states, financially motivated threat actors, transnational criminal organizations, foreign terrorist organizations, and other malicious actors are evolving their methods, incorporating new and emerging technical abilities alongside social media, to conduct malicious activities.
Elements of Multidimensional Threats
Multidimensional threats incorporate tactics, techniques, and procedures (TTPs) from the cyber, physical, and informational domains.
Cyber
The cyber domain consists of technical attacks against networks, systems, and data. It covers threat activity such as network penetration, data extraction, website defacement, Distributed Denial of Service (DDoS) attacks, ransomware, and phishing — along with capabilities enhanced by artificial intelligence (AI).
Physical
Otherwise known as the "kinetic" domain, the physical domain includes activity that can harm people, property, and infrastructure. Physical threats include, but are not limited to, targeted acts of violence, attacks on critical infrastructure, mass shootings, swatting, and human trafficking.
Information Operations
Threat actors manipulate, manufacture, or steal data to maliciously distribute information, often to targeted audiences, as a means of sowing discord, undermining confidence in trusted institutions, and in support of threat actor-specific objectives. This domain includes promoting misleading or false narratives, social engineering, hack-and-leak operations, and deepfakes, including content generated by AI.
Examples of Multidimensional Threats
In today's world, foreign and domestic threat actors leverage the power of the internet to advance their objectives. Here are some examples of what they may look like:
- State-sponsored threats actors conduct cyber attacks with the aim of undermining trust in key institutions, stealing protected information, or causing disruptions to integral services.
- Terrorist organizations post content online to incite and inspire violence.
- Human smugglers/traffickers use social media and other digital platforms to market smuggling services and recruit supporters needs.
- Narcotics cartels turn to internet-based tools to facilitate the manufacturing, shipping, and sale of illicit substances, as well as launder their profits.
