Secure Configurations and the Power of SCAP
By Tony Sager, Senior Vice President, and Chief Evangelist
Have you ever heard of Security Content Automation Protocols (SCAP)? SCAP is a method for using specific standards to help organizations automate vulnerability management and policy compliance evaluation. SCAP comprises numerous open security standards, as well as applications which use these standards to check systems for vulnerabilities and misconfigurations.
An Information Management Challenge
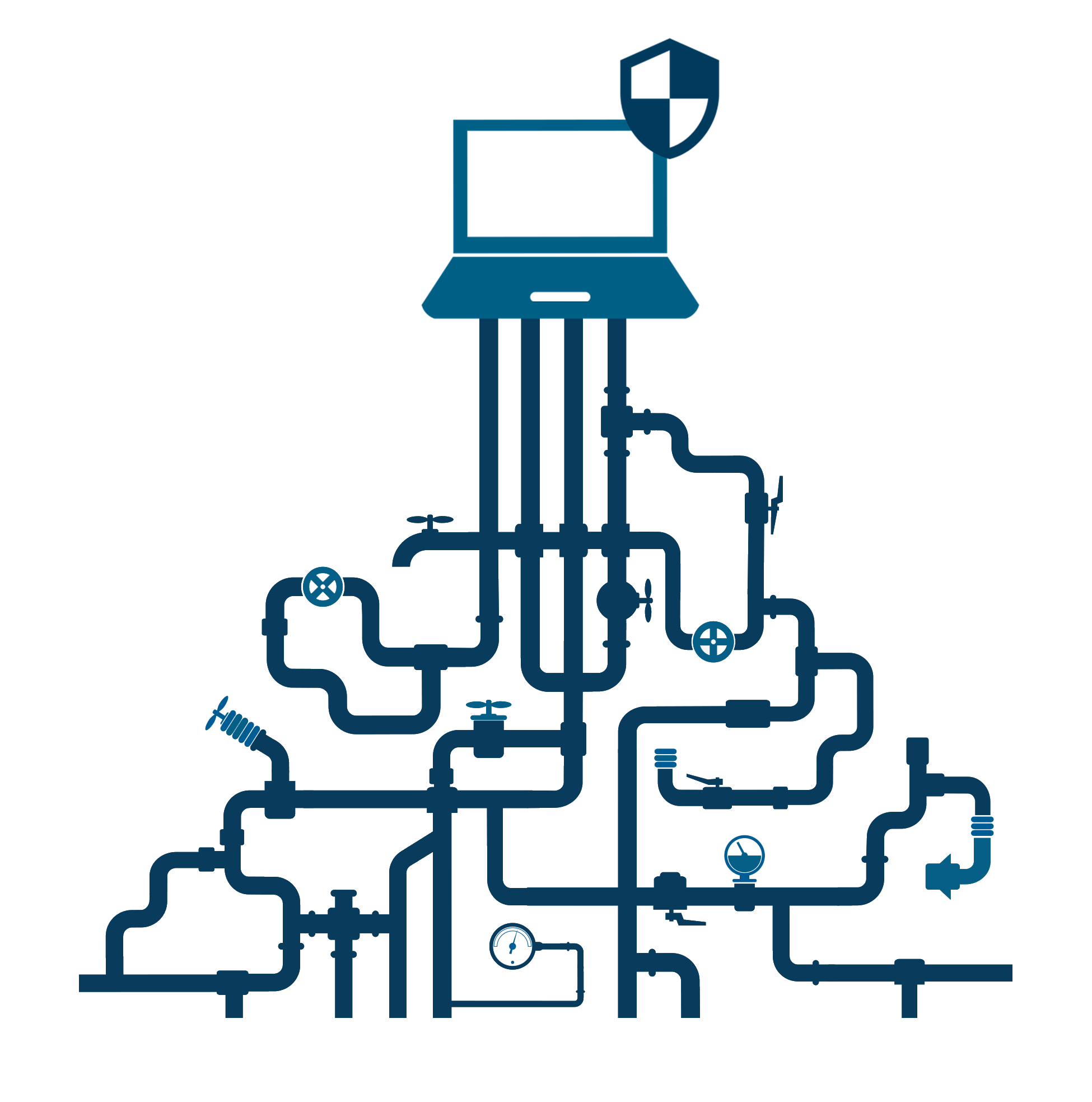 At its heart, cybersecurity is really an information management challenge. That is, how do we move information (like threat indicators, benchmark configurations, or the output of vulnerability scanners) from where it is created to where it is needed (like patch managers and remediation tools), in a form in which it is useful? SCAP defines all of the “plumbing” that allows information to be gathered, moved, and used in a way that is standardized, vendor-neutral, and cost-effective. It really is the cyber equivalent of building and plumbing “codes” that allow cyber defenders and tools to focus on finding and fixing problems, not moving and translating data.
At its heart, cybersecurity is really an information management challenge. That is, how do we move information (like threat indicators, benchmark configurations, or the output of vulnerability scanners) from where it is created to where it is needed (like patch managers and remediation tools), in a form in which it is useful? SCAP defines all of the “plumbing” that allows information to be gathered, moved, and used in a way that is standardized, vendor-neutral, and cost-effective. It really is the cyber equivalent of building and plumbing “codes” that allow cyber defenders and tools to focus on finding and fixing problems, not moving and translating data.
Common Solutions
Because they use common security “plumbing” and terminology, many SCAP-validated applications will:
- Scan systems against open cybersecurity standards
- Report back with a “score” to help evaluate the system’s security posture
- Interoperate with other SCAP-validated scanners to express results in a standardized way
SCAP helps organizations around the world meet regulatory compliance for PCI DSS, NIST, FedRAMP, FISMA, and more by comparing their system settings to those found in popular security guidelines, such as the CIS Benchmarks. The CIS Benchmarks are independent, community-driven configuration recommendations for more than 100 technologies. CIS-CAT Pro, the CIS Configuration Assessment Tool, is among the tools and applications validated by SCAP.[1]
It can help you automate the process of evaluating your systems’ settings to the secure recommendations of the CIS Benchmarks.
What makes SCAP so powerful? I’ve identified three things which set it apart in an industry consumed by flash and noise.
1| Extraordinary cooperation among stakeholders.
No single organization can understand the security problems of all technologies. No single organization sees the full range of ways that cybercriminals attack organizations every day. No single organization can conceive of or test all possible countermeasures. Without single primary authority or funding, security advice practitioners like NSA, DISA, NIST, SANS, and CIS cooperate with government agencies and industry experts to build consensus around key security concepts.
By bringing together key experts, SCAP institutionalizes and guides threat information sharing across government and industry. Each organization brings their own “constituency” of users who either have to follow their recommendations (e.g., DISA STIGs) or choose to follow (e.g., NIST Checklists, NSA Guides, CIS Benchmarks). Users of SCAP-validated applications also bring a “reality check”, counter-balancing security advice with practical operational needs.
2| It’s all about stopping attacks and closing vulnerabilities.
SCAP community discussions are based on deep analysis of the technology as well as years of experience in field testing of operational systems. Combined with threat information from the Intelligence community (via participants such as NSA and DISA), our guidance represents our best translation of vulnerability knowledge into the language of system administration. For example, CIS translates threat knowledge into system configurations (the CIS Benchmarks) that will prevent or stop the spread of many attack vectors. So, installing, managing to, and reporting on CIS Benchmarks is an essential foundation for cyber defense.
In the best scenarios, SCAP coordination leads to:
- Getting government and industry to agree *early* on security, and make it part of the shipped commercial product;
- Building the right wording into procurements and contracts to require security measures;
- ensuring that oversight or governance processes (e.g., FISMA, DIACAP, NIST processes) expect common cybersecurity standards; and
- automating using commercial tools to allow us to manage security processes;
3| SCAP puts standards into action.
Beyond standardization, SCAP defines the technical “plumbing” that allows guidance like the CIS Benchmarks to be expressed in open and machine-readable form, supported by commercial tools, and allows users to draw conclusions about their security posture when working in complex environments comprising many tools from multiple vendors.
SCAP also standardizes, in a machine-processable way, the basic raw data of the business of cybersecurity: naming of flaws in software; tests for the presence of flaws; naming of specific versions of software; status of configuration options (e.g., turn AUTORUN off); and basic configuration policies. This provides us the potential for a dramatically better, more automated, and more integrated environment: information from many types and sources of tools (commercial, net management, security, etc.) can be naturally shared, summarized, and correlated. This includes data from “human sensors” – vulnerabilities witnessed by everyday cyber experts working in the field.
By centering around a common vulnerability language, SCAP provides experts with “global” situational awareness and visibility into data from “local” tools (virus and malware scanners, intrusion event loggers, enterprise management tools, asset tracking tools, configuration managers, …). Users can also manage new information and cyber incidents – meaning “global” requests for information or action can be processed by “local” tools, like CIS-CAT Pro.
 Learn more about CIS-CAT Pro
Learn more about CIS-CAT Pro
The Road Ahead
Improving cybersecurity posture is never an easy journey; but with common security terminology and standardized tools, it is achievable. SCAP validation helps experts coalesce around agreed-upon concepts and techniques, leaving more time to focus on preventing vulnerabilities than naming them.
To follow the latest SCAP community developments, visit The Security Content Automation Protocol (SCAP).