Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter
655 Results Found
Solutions
Industry
531 - 540 of 655 results
Published on 07.09.2019
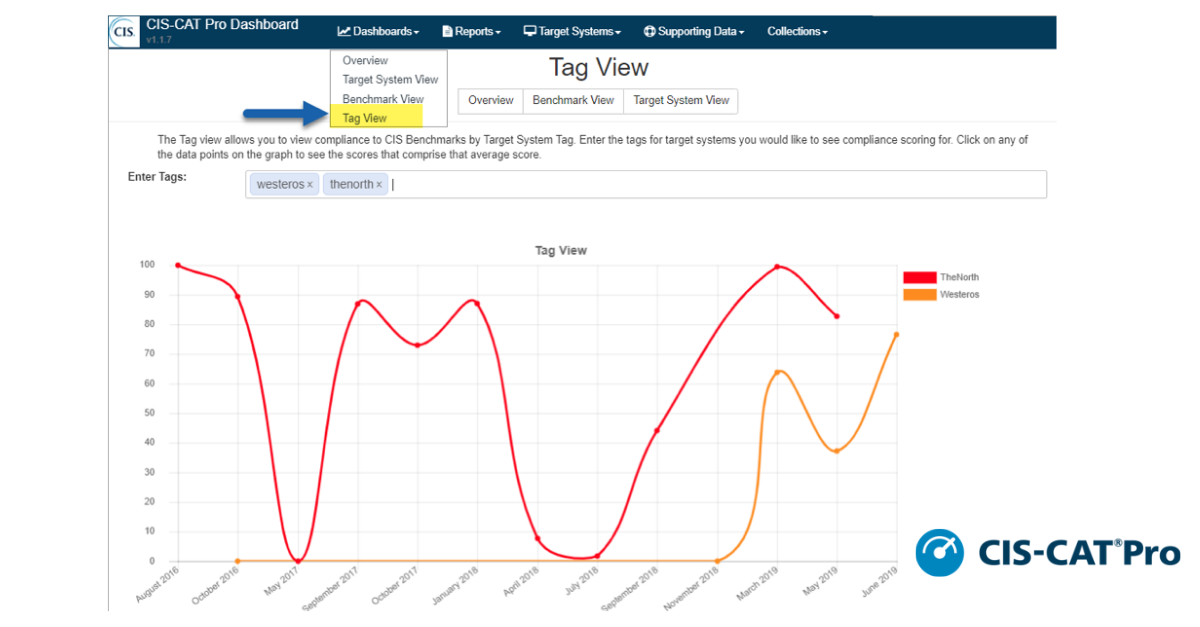
CIS SecureSuite® Members are receiving an update to CIS-CAT Pro Dashboard in v1.1.7. CIS-CAT Pro Dashboard is the companion tool to CIS-CAT Pro A...
CIS BenchmarksCIS SecureSuite
Published on 07.03.2019
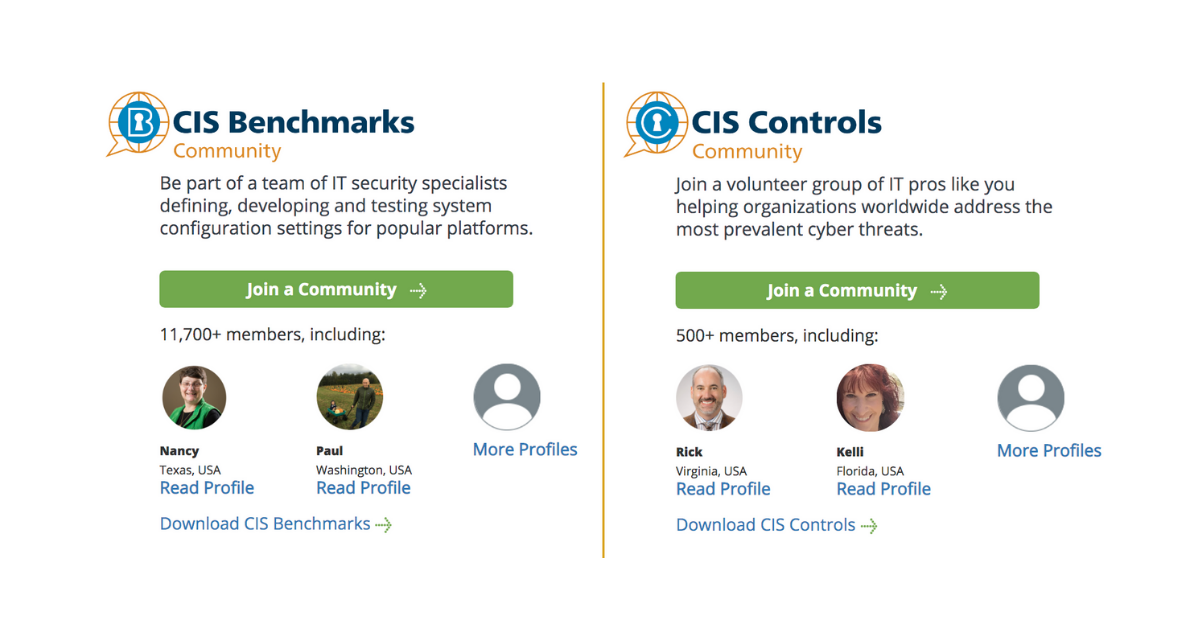
Have you ever wanted to be part of a global security community? Want to help develop cybersecurity recommendations for new and emerging technolog...
CIS Benchmarks
Published on 07.02.2019
The CIS® team had a great experience at AWS re:Inforce from June 25-26, 2019 in Boston, MA. As AWS’ inaugural security conference, re:Inforce bro...
CIS Hardened ImagesCIS SecureSuite
Published on 06.27.2019
Internet of Things (IoT) devices aren’t just invading our homes; these smart, connected machines have taken root in the workplace. And they’re he...
CIS Controls
Published on 06.20.2019
The CIS team is heading to Boston, Massachusetts on June 25-26, 2019 for AWS re:Inforce. This inaugural cloud security event will bring together ...
CIS Hardened Images
Published on 06.18.2019
The CIS Benchmarks team is excited to announce the release of our newest browser security recommendations. CIS Google Chrome Benchmark v2.0.0 con...
CIS BenchmarksCIS SecureSuite
Published on 06.14.2019
The CIS team wrapped up a great week at AWS Public Sector Summit in Washington, DC. In addition to spreading the word about CIS at our booth on t...
CIS Hardened Images
Published on 06.11.2019
Cyber threats target public sector organizations every day. From ransomware attacks to data theft, systems need defense-in-depth best practices a...
Published on 06.04.2019
Operating systems, containers, and servers ship with insecure default settings, leaving gaps that cybercriminals can take advantage of. That’s wh...
CIS BenchmarksCIS SecureSuite
Published on 05.14.2019
The CIS team will be heading to Washington, DC on June 11-12 for AWS Public Sector Summit. We’ll be speaking about CIS Benchmarks, CIS Hardened I...
CIS BenchmarksCIS Hardened Images
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More