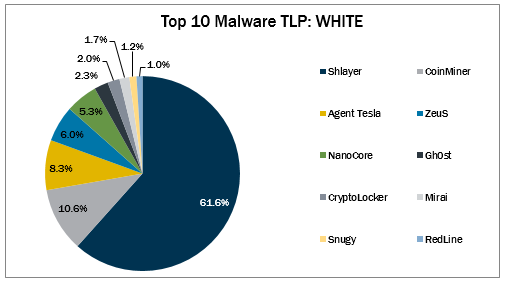
Top 10 Malware January 2022
In January 2022, the Top 10 stayed consistent with the previous month with the exception of CryptoLocker and Snugy. Snugy returned to the Top 10, while CryptoLocker made its first appearance. CryptoLocker is a ransomware that was originally spread via email and the Gameover ZeuS botnet, but once the botnet was taken down, the encryption key was released. Since then, multiple variants have spawned, which are capable of encrypting files and are known for fully renaming files and appending them with a random extension, .encrypted, or .cryptolocker depending on the variant. These variants, although similar, are spread through numerous ways and may have varying capabilities. The Top 10 Malware variants comprise 69% of the total malware activity in January 2022, increasing 7% from December 2021.

Malware Infection Vectors
The MS-ISAC tracks potential primary infection vectors for our Top 10 Malware each month based on open-source reporting, as depicted in the graph below. We currently track four initial infection vectors: Dropped, Malvertisement, Malspam, and Network. Some malware employ different vectors in different contexts and are thus tracked as Multiple.
In January 2022, Malvertisement accounted for the greatest number of alerts. Malvertisement remains the top initial infection vector due to Shlayer activity. Activity levels for all initial infection vectors increased, except for Dropped, which decreased by 33%. It is likely that Malvertisement will remain the primary infection vector as the Shlayer campaign continues. The Multiple category increases and decreases seemingly sporadically, making it difficult to predict trends. Albeit, it will likely continue to make up a significant portion of the initial infection vectors as malware becomes more sophisticated and employs multiple methods to infect systems. Malspam consistently represents a portion of the Top 10 malware as it is one of the oldest and most reliable primary initial infection vectors used by cyber threat actors in both this category and the Multiple category.
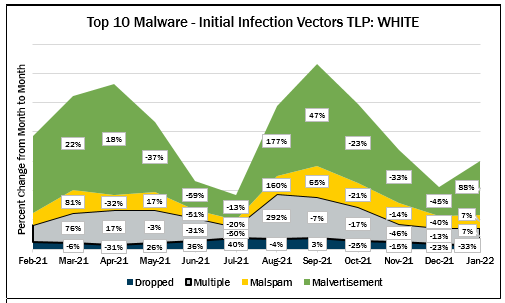
Dropped – Malware delivered by other malware already on the system, an exploit kit, infected third-party software, or manually by a cyber threat actor. Gh0st and Mirai use this technique
Multiple – Malware that currently favors at least two vectors. Currently, CoinMiner, CryptoLocker, RedLine, and ZeuS are the malware utilizing multiple vectors.
Malspam – Unsolicited emails either direct users to malicious web sites or trick users into downloading or opening malware. Top 10 Malware using this technique include Agent Tesla, NanoCore, and Snugy.
Malvertisement – Malware introduced through malicious advertisements. Currently, Shlayer is the only Top 10 Malware using this technique.
Top 10 Malware and IOCs
Below are the Top 10 Malware ranked in order of prevalence. The respective indicators of compromise (IOCs) are provided to aid in detecting and preventing infections from these Top 10 Malware variants. Note: The associated URIs are aligned with malware’s respective domain(s) or IP(s) and increase the likelihood of maliciousness when found together. The URIs alone are not inherently malicious.
1. Shlayer
Shlayer is a downloader and dropper for MacOS malware. It is primarily distributed through malicious websites, hijacked domains, and malvertizing posing as a fake Adobe Flash updater.
All Shlayer domains follow the same pattern <api.random_name.com>. Below area several examples of domains Shlayer uses.
Domains
- api[.]interfacecache[.]com
- api[.]scalableunit[.]com
- api[.]typicalconfig[.]com
- api[.]standartanalog[.]com
- api[.]fieldenumerator[.]com
- api[.]practicalsprint[.]com
- api[.]searchwebsvc[.]com
- api[.]connectedtask[.]com
- api[.]navigationbuffer[.]com
- api[.]windowtask[.]com
2. CoinMiner
CoinMiner is a cryptocurrency miner family that typically uses Windows Management Instrumentation (WMI) and EternalBlue to spread across a network. Additionally, it typically uses the WMI Standard Event Consumer scripting to execute scripts for persistence. However, due to multiple variants of this malware, capabilities may vary. CoinMiner spreads through malspam or is dropped by other malware.
3. Agent Tesla
Agent Tesla is a RAT that exfiltrate credentials, log keystrokes, and capture screenshots from an infected computer.
4. ZeuS
ZeuS is a modular banking trojan which uses keystroke logging to compromise victim credentials when the user visits a banking website. Since the release of the ZeuS source code in 2011, many other malware variants have adopted parts of its codebase, which means that events classified as ZeuS may actually be other malware using parts of the ZeuS code.
5. NanoCore
NanoCore is a RAT spread via malspam as a malicious Excel XLS spreadsheet. As a RAT, NanoCore can accept commands to download and execute files, visit websites, and add registry keys for persistence.
6. Gh0st
Gh0st is a RAT used to control infected endpoints. Gh0st is dropped by other malware to create a backdoor into a device that allows an attacker to fully control the infected device.
7. CryptoLocker
CryptoLocker is a ransomware that was originally spread via email and the Gameover ZeuS botnet, but once the botnet was taken down, the encryption key was released. Since then, multiple variants have spawned, which are capable of encrypting files and are known for fully renaming files and appending them with a random extension, .encrypted, or .cryptolocker depending on the variant. These variants, although similar, are spread through numerous ways and may have varying capabilities.
8. Mirai
Mirai is a malware botnet known to compromise Internet of Things (IoT) devices in order to conduct large-scale DDoS attacks. Mirai is dropped after an exploit has allowed the attacker to gain access to a machine.
9. Snugy
Snugy is a PowerShell-based backdoor allowing the attacker to obtain the system’s hostname and to run commands. This backdoor communicates through a DNS tunneling channel on the compromised server.
10. RedLine,
RedLineis an infostealer available for purchase on cyber-criminal forums. Campaigns, targets, infection vectors and capabilities vary based on the version purchased. The malware typically targets information that can be easily monetized, such as credentials, cookies, banking information, and cryptocurrency wallet information. Additionally, the malware gathers information about the infected system such as web-browser, FTP clients, instant messengers, VPN services, and gaming clients. Furthermore, RedLine has remote functionality allowing it to download further malicious tools or drop
As of June 23, 2025, the MS-ISAC has introduced a fee-based membership. Any potential reference to no-cost MS-ISAC services no longer applies.
