All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1378 Results Found
Solutions
Industry
931 - 940 of 1378 results
Published on 01.22.2021
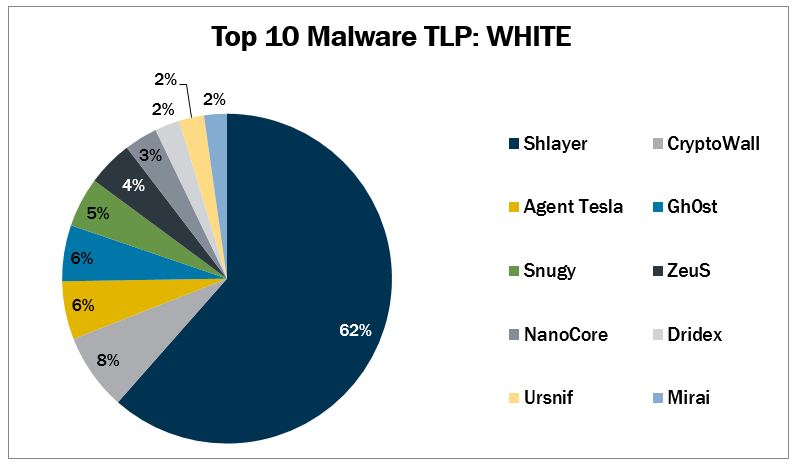
In December 2020, the MS-SIAC observed 4 malware (CryptoWall, NanoCore, Ursnif, and ZeuS) return to the Top 10. The Top 10 Malware variants compo...
Published on 01.19.2021
Previously presented on February 11, 2021 | 3:00 pm EST What Attendees Learned: A discussion of the big three open source Content Management Syst...
MS-ISAC
Published on 01.19.2021
By: Kathleen M. Moriarty, CIS Chief Technology Officer We are on a path that will see information security transformed in the next 5-10 years. Th...
CIS BenchmarksCIS Controls
Published on 01.15.2021
In 2020, the Center for Internet Security (CIS) recently celebrated its 20thyear of creating confidence in the connected world. In preparation fo...
CIS BenchmarksCIS ControlsCIS CyberMarketCIS Hardened ImagesCIS Services
Published on 01.15.2021
What it is Endpoint Detection and Response (EDR) is security software that is deployed on workstations and servers, commonly referred to as “endp...
Published on 01.14.2021
While few people foresaw the dramatic developments of the past year, CIS experts interviewed in 2020 identified several cybersecurity trends that...
Published on 01.12.2021
Secure configurations are a key best practice for limiting an organization’s cyber vulnerabilities. Since systems don’t ship securely, it’s impor...
CIS BenchmarksCIS SecureSuite
Published on 01.06.2021
CIS is excited to announce the release of the following CIS Benchmarks. These CIS Benchmark releases would not have been possible without the tim...
CIS SecureSuite
Published on 01.06.2021
Ransomware attacks targeting U.S. State, Local, Tribal, and Territorial government entities (SLTTs) have been on the rise since 2018. It is essen...
CIS Services
Published on 12.22.2020
In November 2020, the MS-ISAC observed four malware (Dridex, Kovter, Mirai, and Qakbot) return to the Top 10, as well as two new variants (Ngiowe...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More