All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1377 Results Found
Solutions
Industry
711 - 720 of 1377 results
Published on 03.29.2022
Episode 27 focuses on the common cyber scams malicious actors have been using for decades and offer advice for dealing with them.
Published on 03.28.2022
Making security simpler as controls become integrated into organizations' zero-trust journeys is a tremendous opportunity for democratizing secur...
Published on 03.28.2022
Scale is the most important consideration as industry transforms information security and assurance across our supply chains.
Published on 03.25.2022
Instruction for applying best practices to enterprise systems.
CIS Controls
Published on 03.25.2022
The CIS Critical Security Controls (CIS Controls) team has created guide to help organizations create secure cloud environments.
CIS Controls
Published on 03.22.2022
A new CIS Benchmark was created to offer added protection for election management system gateway machines.
CIS Benchmarks
Published on 03.17.2022
CIS's SOC 2 Type II compliance ensures members’ data and associated information is protected at all times with all compliance requirements.
CIS Controls
Published on 03.15.2022
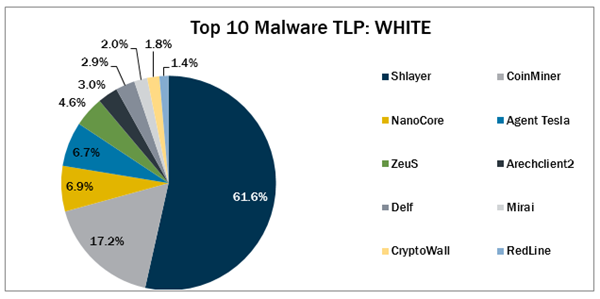
In February 2022, Arechlient2, CryptoWall, and Delf. CryptoWall returned to the Top 10, while Arechclient2 and Delf made their first appearances.
Published on 03.11.2022
In episode 26 of Cybersecurity Where You Are, Tony Sager and guest Brian Hajost of SteelCloud discuss issues around secure configuration manageme...
Published on 03.11.2022
SLTT Perspectives to Inform the State and Local Cybersecurity Grant Program
MS-ISAC
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More

.png?h=313&iar=0&w=600&rev=7206e533fcb94f09ab8c6137aa0a770e&hash=E8A74A375604DD2C5C9EA7BBBCF6DBE9)