All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter
1387 Results Found
Solutions
Industry
1211 - 1220 of 1387 results
Published on 10.22.2018
By Sean Atkinson, Chief Information Security Officer The Department of Homeland Security (DHS) has defined 16 critical infrastructure sectors in ...
CIS Controls
Published on 10.18.2018
In an effort to be fully prepared for a cyber incident, it’s important for key members in an organization to know the proper steps to take when h...
MS-ISAC
Published on 10.18.2018
Tabletop exercises to help cybersecurity teams develop tactical strategies for securing their systems.
MS-ISAC
Published on 10.16.2018
CIS SecureSuite® Members can now customize CIS Benchmarks™ within the CIS WorkBench platform. This added flexibility will help users tailor secur...
CIS SecureSuite
Published on 10.15.2018
The CIS Controls are a prioritized set of actions that collectively form a defense-in-depth set of cybersecurity best practices. Together, they m...
CIS Controls
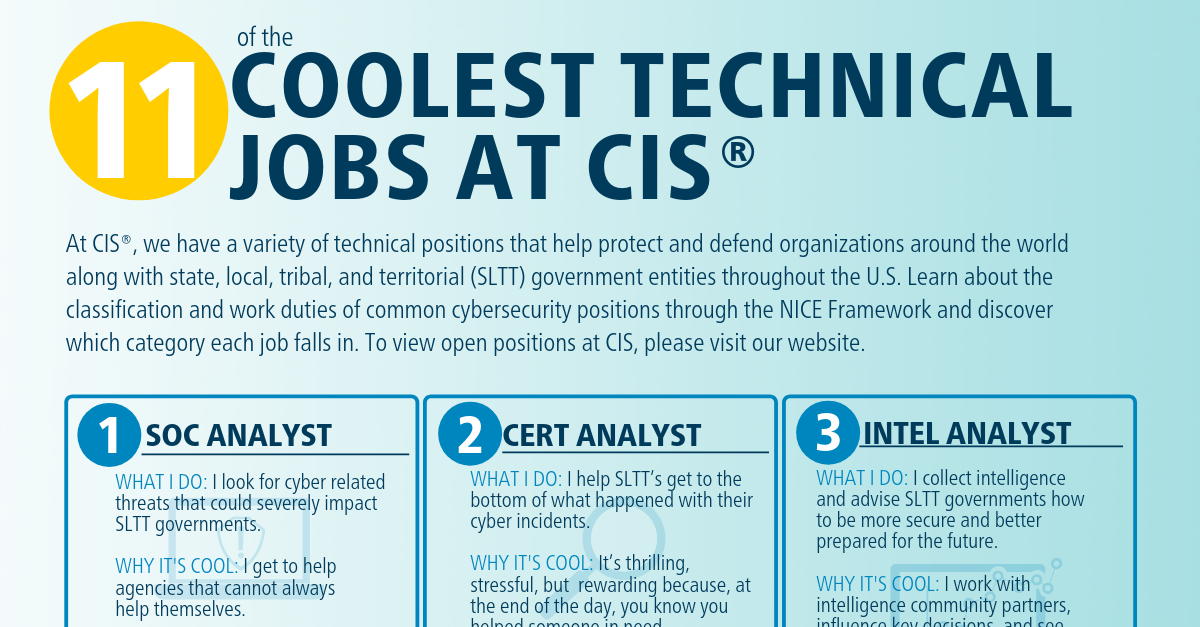
Published on 10.11.2018
There are hundreds of different technical jobs in the cybersecurity industry, with millions of unfilled positions around the globe. Each position...
CIS BenchmarksCIS ControlsCIS CyberMarketCIS Hardened ImagesCIS Services
Published on 10.09.2018
This summary report describes key findings from the 2017 NCSR.
MS-ISAC
Published on 10.09.2018
To celebrate this week’s theme of ‘Educating for a Career in Cybersecurity’ during Cybersecurity Awareness Month (CSAM), we wanted to get an insi...
CIS BenchmarksCIS ControlsCIS CyberMarketCIS Hardened ImagesCIS Services
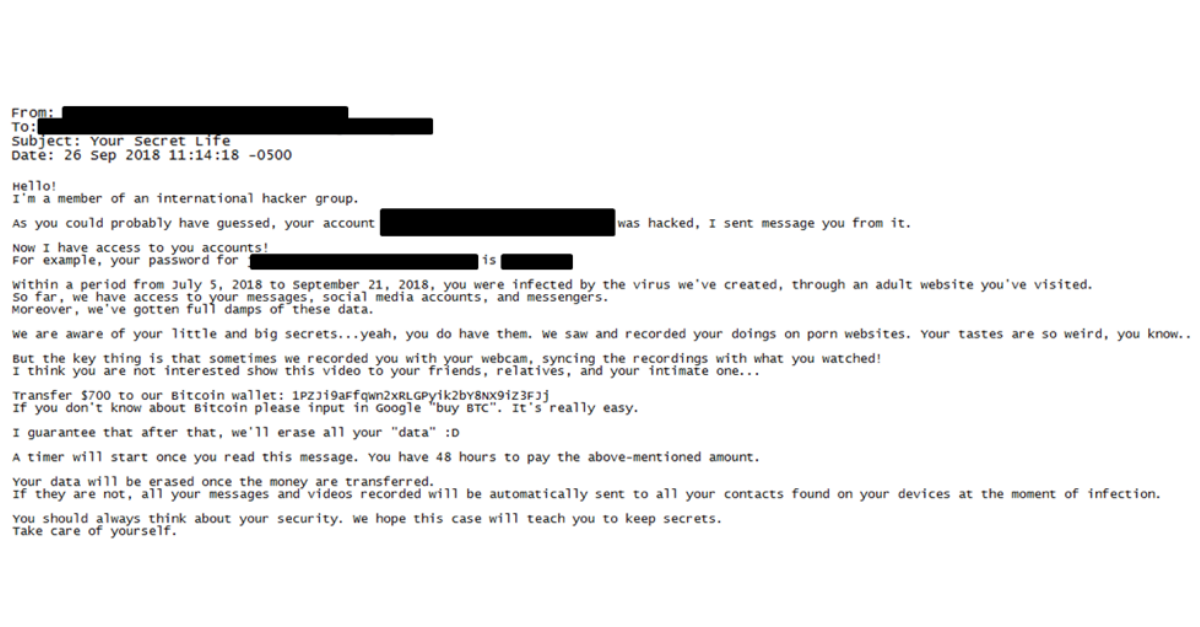
Published on 10.04.2018
Sextortion hoax scams continue to affect state, local, tribal, and territorial (SLTT) government employees, who are reporting updated email tacti...
MS-ISAC
Published on 10.02.2018
What it is A web attack targets vulnerabilities in websites to gain unauthorized access, obtain confidential information, introduce malicious con...
MS-ISAC
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More