Explanation of the Current Alert Level of GUARDED
The alert level is the overall current threat level.
On April 17, the Cyber Threat Alert Level was evaluated and is remaining at Blue (Guarded) due to vulnerabilities in Google, Palo Alto, Mozilla, and Google products. On April 10, the MS-ISAC released an advisory for multiple vulnerabilities in Google Chrome, the most severe of which could allow for arbitrary code execution. On April 12, the MS-ISAC released an advisory for a vulnerability in Palo Alto PAN-OS that could allow for arbitrary code execution. On April 16, the MS-ISAC released an advisory for multiple vulnerabilities in Mozilla products, the most severe of which could allow for arbitrary code execution. On April 17, the MS-ISAC released an advisory for multiple vulnerabilities in Google Chrome, the most severe of which could allow for remote code execution. Organizations and users are advised to update and apply all appropriate vendor security patches to vulnerable systems and to continue to update their antivirus signatures daily. Another line of defense includes user awareness training regarding the threats posed by attachments and hypertext links contained in emails especially from un-trusted sources.
Latest Advisory
Our MS-ISAC Advisories
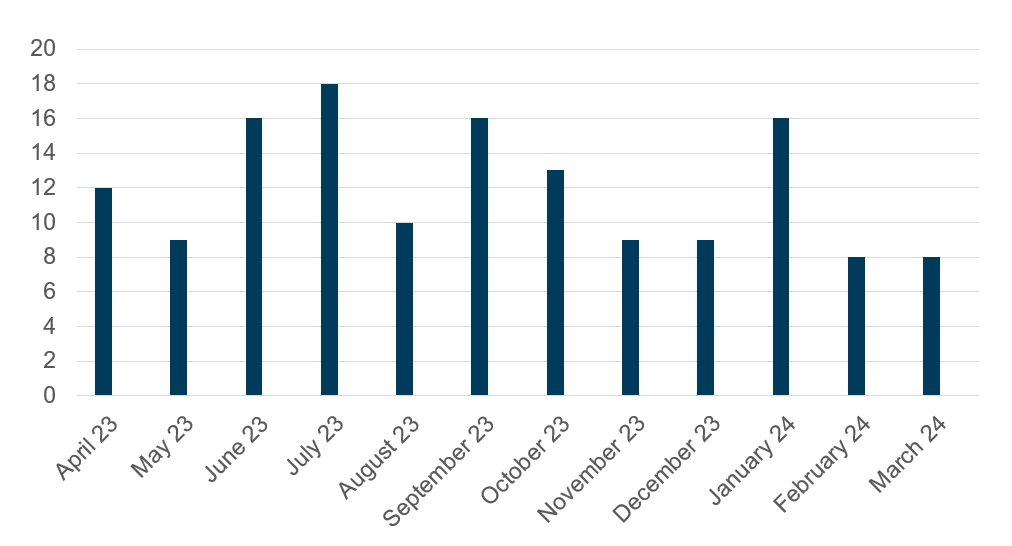
Advisories Released (Last 12 Months)
In Q4 2023, the Top 10 Malware observed at the Multi-State Information Sharing and Analysis Center (MS-ISAC®) changed slightly from the previous quarter. Arechclient2 climbed from eighth to the second spot, while ReverseRAT and Pegasus replaced Fake Browser and Ratenjay. This was Pegasus’s first appearance on the Top 10 Malware list. SocGholish was the most observed malware in Q4 again, comprising 60% of Top 10 Malware incidents. SocGholish maintained its top position by leveraging fake browser updates. Additionally, the second and third most prevalent malware were .Net-based Remote Access Trojans (RATs).
Top Malware Q4 2023
- SocGholish
- Arechclient2
- Agent Tesla
- CoinMiner
- NanoCore
- RogueRaticate
- ViperSoftX
- ReverseRAT
- Gh0st
- Pegasus
Take Control of Your Organization's Security

The information on this page is maintained by our Security Operations Center, which is part of MS-ISAC and EI-ISAC.

