CIS Offers New Guidance to Public & Private Businesses on Email-Related Scams in December 5 Manhattan Workshop
November 28, 2017
Albany, NY
Session Designed to Combat Increasingly Pervasive Phishing Attacks Responsible for More than $5 Billion in Fraud
Helping global organizations align for a new wave of phishing attacks and Business Email Compromise (BEC), CIS (the Center for Internet Security) today unveiled new guidance to help global industries combat new security threats impacting 131 countries and creating more than $5 billion in fraud. A non-profit organization helping to safeguard private and public companies against cyber threats, CIS announced a BEC Workshop from 8:30 a.m. to 12:30 p.m. on December 5 at the Public Theatre, 425 Lafayette Street in Manhattan as part of an ongoing initiative to protect organizations and individuals from emerging email schemes. The FBI, the U.S. Secret Service and multiple information sharing analysis centers will also offer guidance on avoiding BEC at the workshop. For more information visit the National Health Information Sharing & Analysis Center.
BEC cons, also referred to as man-in-the email attacks, are sophisticated email- and electronic communication based-scams through which attackers gain access to or impersonate a business executive, employee, or other person to defraud the company, customers or partners. Attacks are often used to solicit payments or retrieve funds, such as bogus invoicing scams or those geared toward gaining access to employee payroll and W2 information. Since October 2013, the Federal Bureau of Investigation has identified victims from 131 countries and a global monetary exposure of more than $5 billion related to BEC fraud.
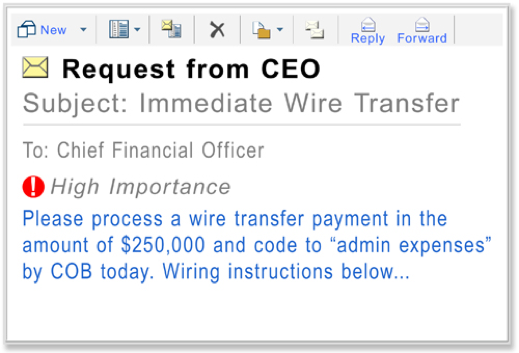 “Phishing attacks come from two core sources: a compromised account, whereby an authorized user’s account was hacked, or from a fraudulent account set up to resemble an authorized user,” said Brig. Gen. Steven J. Spano, President & COO, CIS. “No matter which method is used – the impact is significant and the repercussions can be devastating.”
“Phishing attacks come from two core sources: a compromised account, whereby an authorized user’s account was hacked, or from a fraudulent account set up to resemble an authorized user,” said Brig. Gen. Steven J. Spano, President & COO, CIS. “No matter which method is used – the impact is significant and the repercussions can be devastating.”
“Compromised business email activity is a growing problem plaguing both the public and private sectors,” said Thomas Duffy, Senior Vice President, Operations and Services chair of the Multi-State Information Sharing & Analysis Center® (MS-ISAC®). “No organization is immune from email scams, emphasizing the need for good cyber hygiene practices across the board.”
The workshop aims to educate attendees on BEC more broadly, as well as the current threat landscape and popular criminal tactics, techniques and procedures. Protection-based strategies will also be discussed, as will the need for creating situational awareness and sharing threat information across departments and agencies.
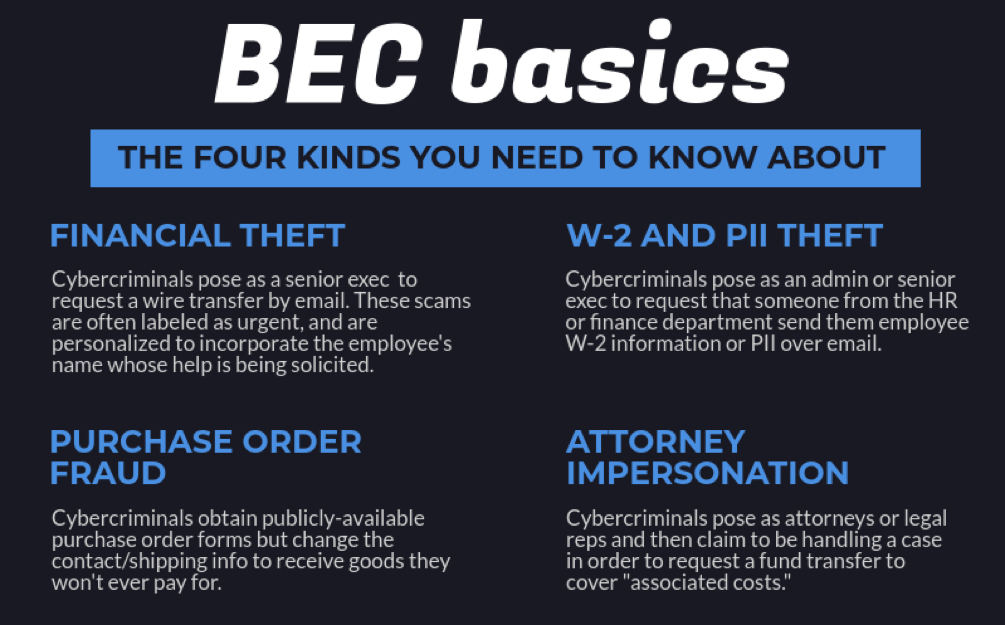
CIS is the home of the MS-ISAC, the Department of Homeland Security’s resource for collaborative cyber information sharing and analysis among state, local, tribal and territorial (SLTT) government entities. CIS has identified four different variants of which organizations should be aware, including Financial Theft, W-2 and Personally Identifiable Information (PII) Data Theft, Purchase Order Fraud, and Attorney Impersonation.
Spano continued, “Keeping your organization or business safe requires a multi-pronged approach. Training is first and foremost and should be given to staff at all levels. Equally important, however, is crafting a policy explaining the risks and then implementing appropriate email filters,” he said.
About the Center for Internet Security
The Center for Internet Security (CIS) is a forward-thinking, non-profit entity that harnesses the power of a global IT community to safeguard private and public organizations against cyber threats. Our CIS Controls and CIS Benchmarks are the global standard and recognized best practices for securing IT systems and data against the most pervasive attacks. These proven guidelines are continuously refined and verified by a volunteer, global community of experienced IT professionals. CIS is home to the Multi-State Information Sharing & Analysis Center® (MS-ISAC), the go-to resource for cyber threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial government entities. To learn more, visit CISecurity.org or follow us on Twitter: @CISecurity.