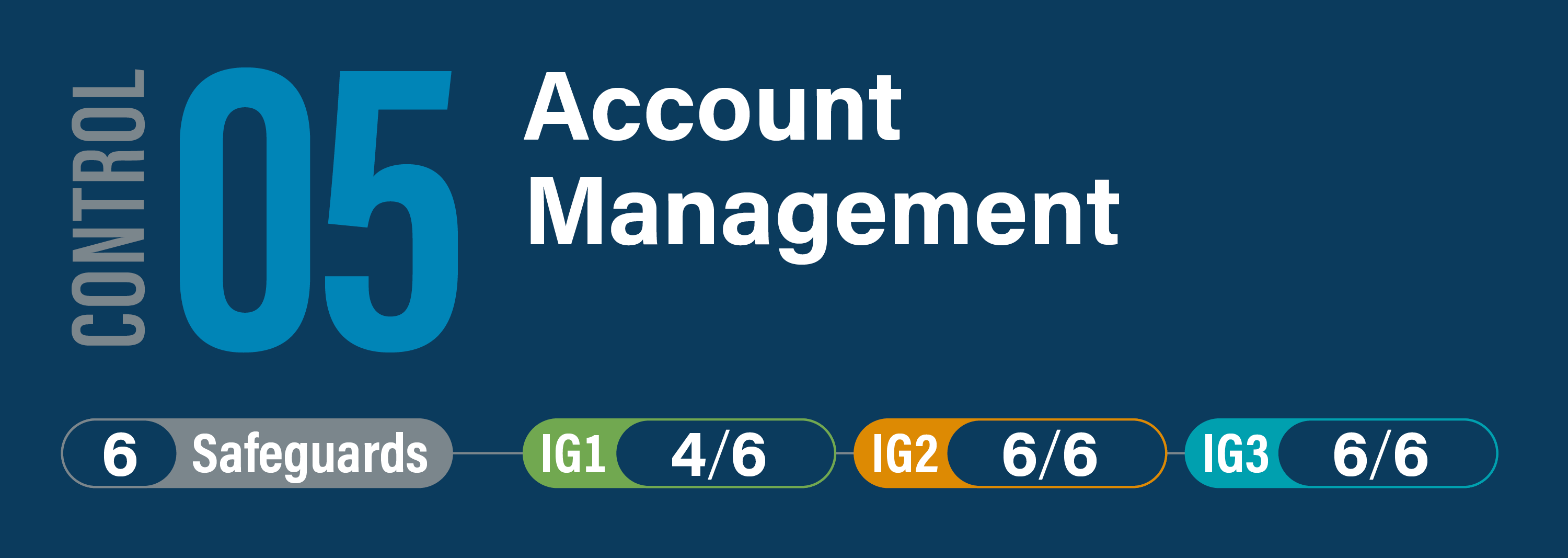
CIS Critical Security Control 5: Account Management
Overview
Use processes and tools to assign and manage authorization to credentials for user accounts, including administrator accounts, as well as service accounts, to enterprise assets and software.