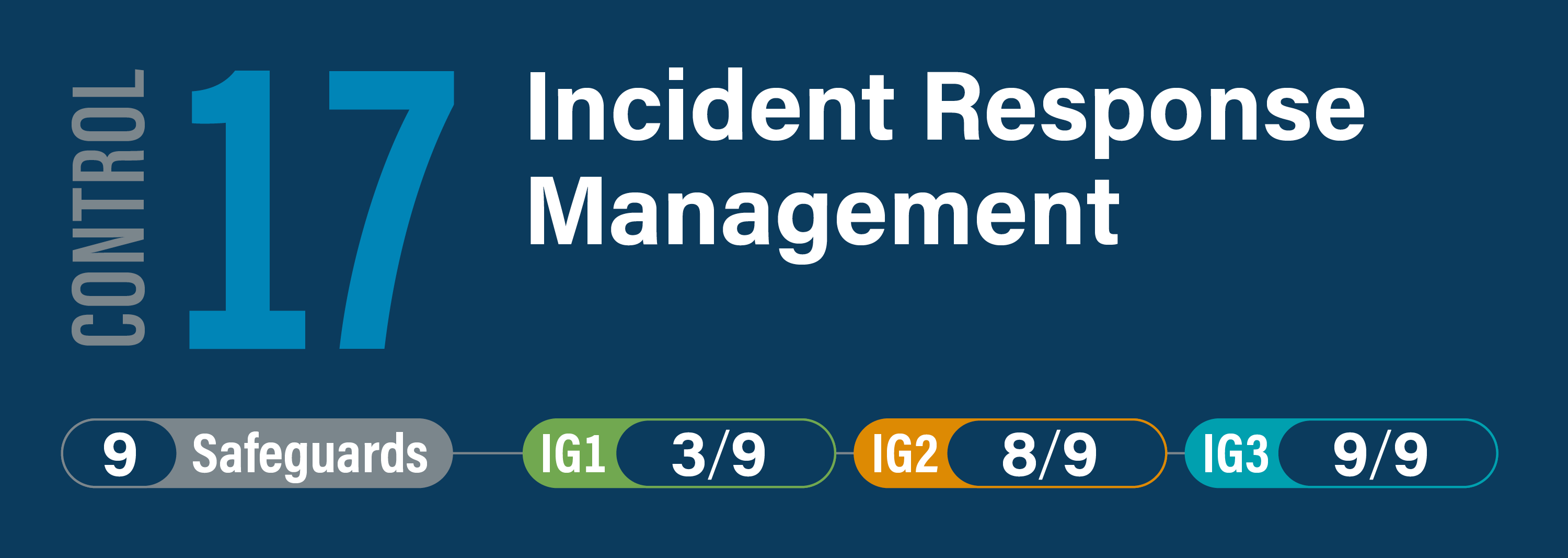
CIS Critical Security Control 17: Incident Response and Management
Overview
Establish a program to develop and maintain an incident response capability (e.g., policies, plans, procedures, defined roles, training, and communications) to prepare, detect, and quickly respond to an attack.