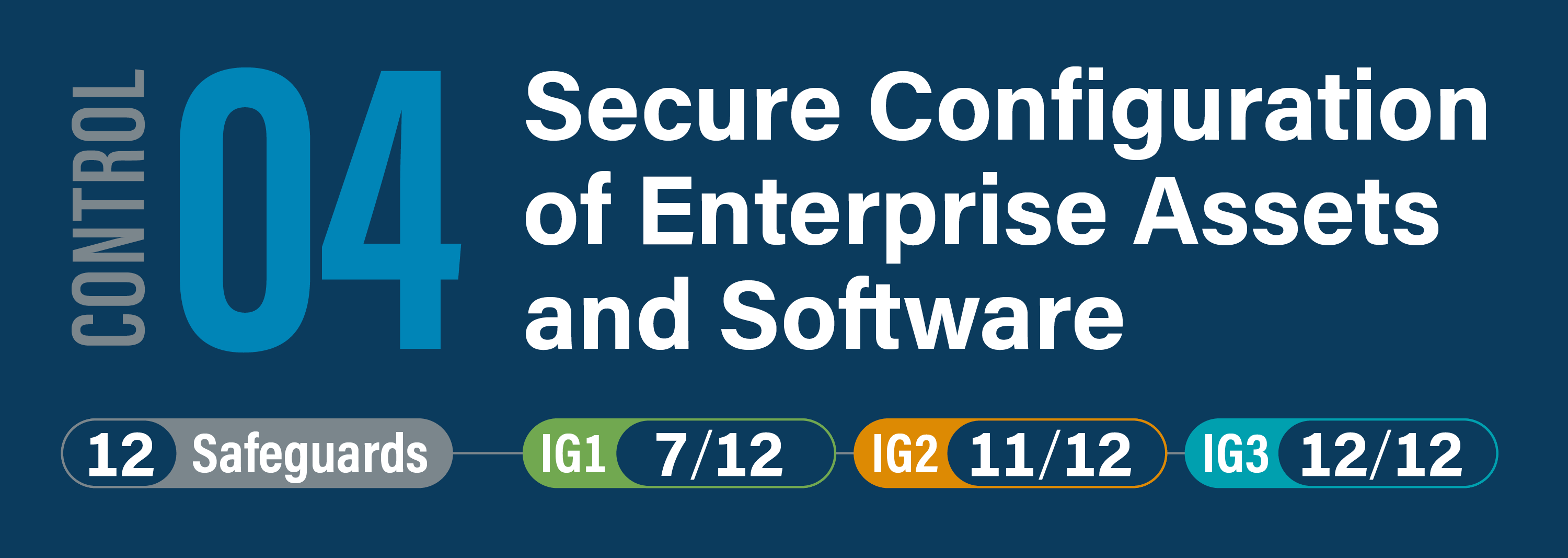
CIS Critical Security Control 4: Secure Configuration of Enterprise Assets and Software
Overview
Establish and maintain the secure configuration of enterprise assets (end-user devices, including portable and mobile; network devices; non-computing/IoT devices; and servers) and software (operating systems and applications).