Showing results 1 - 20 of 1090 for "all"
WHITE PAPER - https://www.cisecurity.org/insights/white-papers/cis-2020-year-in-review
CIS 2020 Year in Review
The Center for Internet Security’s 2020 Year in Review highlights all the efforts the cybersecurity nonprofit accomplished in its 20th year in busines...
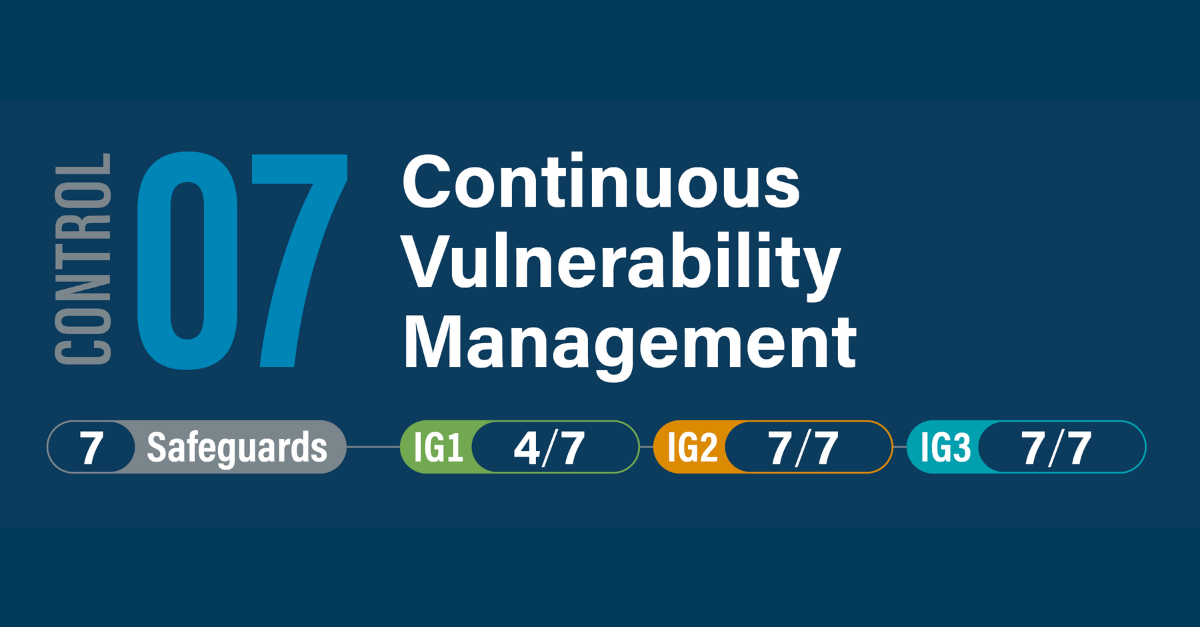
PAGE - https://www.cisecurity.org/controls/continuous-vulnerability-management
CIS Critical Security Control 7: Continuous Vulnerability Management
Overview Develop a plan to continuously assess and track vulnerabilities on all enterprise assets within the enterprise’s infrastructure, in order to ...
PAGE - https://www.cisecurity.org/ms-isac/ms-isac-membership-faq
MS-ISAC® Membership FAQ
Who can join the MS-ISAC? Membership is open to all U.S. SLTT government entities. Who are the members? The MS-ISAC currently includes representatives...
MEDIA MENTION - https://www.cisecurity.org/about-us/media/media-mention/this-is-how-it-was-all-supposed-to-...
‘This is how it was all supposed to work’: The EI-ISAC readies for Election Day
In the months leading up to the election, the Center for Internet Security has also been rolling out new products for its EI-ISAC and MS-ISAC members....
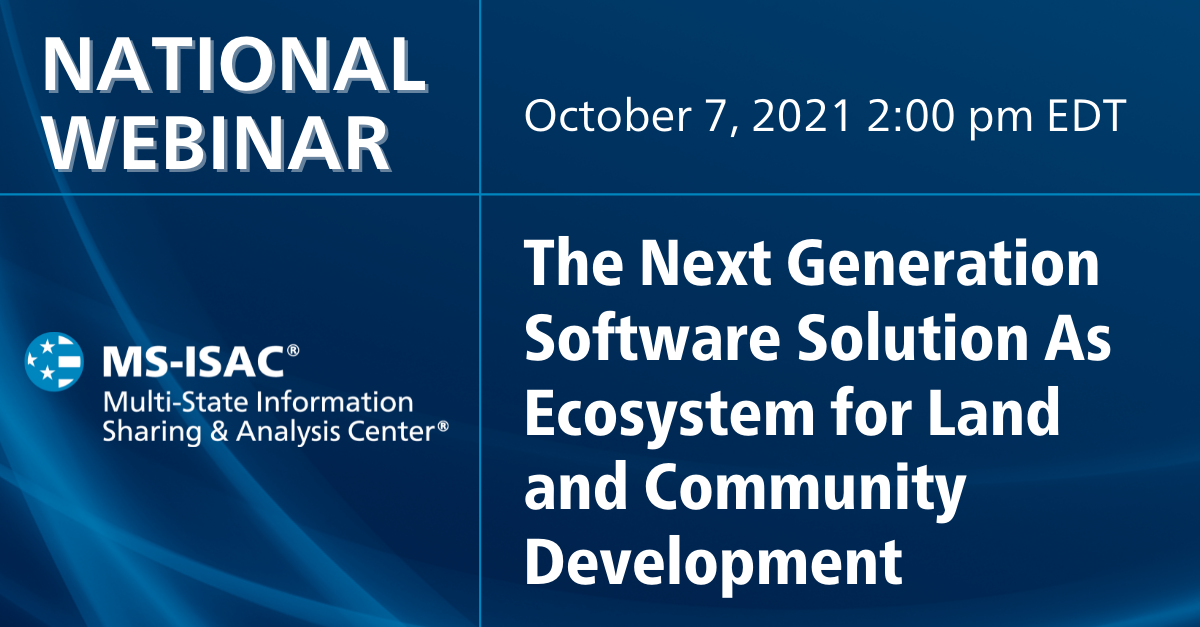
WEBINAR - https://www.cisecurity.org/insights/webinar/isac-national-webinar-the-next-generation-softw...
ISAC National Webinar: The Next Generation Software Solution As Ecosystem for Land and Community Development
Previously presented on Thursday, October 7th | 2:00 pm EDT The COVID-19 pandemic has fundamentally changed how land-management and community-developm...
PAGE - https://www.cisecurity.org/controls/inventory-and-control-of-enterprise-assets
CIS Critical Security Control 1: Inventory and Control of Enterprise Assets
Overview Actively manage (inventory, track, and correct) all enterprise assets (end-user devices, including portable and mobile; network devices; non-...
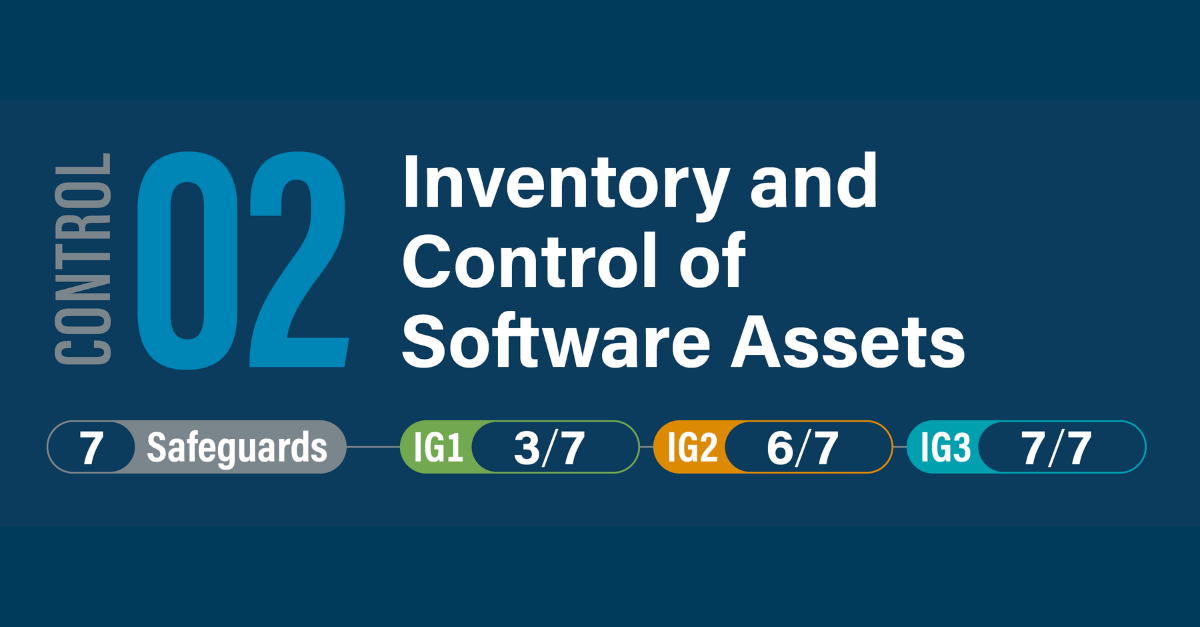
PAGE - https://www.cisecurity.org/controls/inventory-and-control-of-software-assets
CIS Critical Security Control 2: Inventory and Control of Software Assets
Overview Actively manage (inventory, track, and correct) all software (operating systems and applications) on the network so that only authorized soft...
SPOTLIGHT - https://www.cisecurity.org/insights/spotlight/cybersecurity-spotlight-social-engineering
Election Security Spotlight – Social Engineering
What is it Social engineering is the use of deception to manipulate individuals into providing a particular response, generally for a fraudulent or ma...
WHITE PAPER - https://www.cisecurity.org/insights/white-papers/guide-to-enterprise-assets-and-software
Guide to Enterprise Assets and Software
Adopters of the CIS Controls should use this guide as a reference during activities such as implementation or auditing to verify that all in-scope ass...
MEDIA MENTION - https://www.cisecurity.org/about-us/media/media-mention/phishing-disinformation-top-2024-el...
Phishing, Disinformation Top 2024 Election Security Concerns
A new study finds those areas are high on the list of election-related cybersecurity concerns, but public awareness campaigns, training for staff, tab...
PAGE - https://www.cisecurity.org/about-us/leadership/gina-chapman
Gina Chapman
Senior Vice President and General Manager of Sales and Business Services As Senior Vice President and General Manager of Sales and Business Services, ...
MEDIA MENTION - https://www.cisecurity.org/about-us/media/media-mention/cybersecurity-in-education-k-12-wit...
Cybersecurity in Education (K-12) with the CIS Controls
All institutions should take steps to secure their environments. The best way to do this is to follow the proven guidance of the CIS Controls....
MEDIA MENTION - https://www.cisecurity.org/about-us/media/media-mention/the-new-cis-community-defense-model...
The New CIS Community Defense Model, CDM, Brings Security Within the Grasp of All Small Organizations
The CDM moves cybersecurity within closer reach for many who may otherwise choose other unproven methods....
MEDIA MENTION - https://www.cisecurity.org/about-us/media/media-mention/how-we-prepared-for-the-2020-electi...
How We Prepared for the 2020 Election During a Pandemic
The EI-ISAC consists of all 50 states and thousands of local election offices as members, allowing election officials to stay connected and manage ris...
PRESS RELEASE - https://www.cisecurity.org/about-us/media/press-release/center-for-internet-security-funds-...
Center For Internet Security Funds No-Cost Service to Help Protect all U.S. Private Hospitals Against Ransomware
The Malicious Domain Blocking and Reporting Service is also available to all U.S. public hospitals via no-cost membership in the MS-ISAC....
PAGE - https://www.cisecurity.org/services/cis-cybermarket/vendor-information
Vendor Information
Opportunity Process Get an inside look at how the CIS CyberMarket identifies products and services that help meet the needs of MS-ISAC members and oth...